Understanding the Concepts of Privacy and Anonymity with Trezor Coinjoin
Gain control and protect your digital assets with Trezor Coinjoin, the ultimate solution to enhance your privacy and anonymity in the cryptocurrency world.
Privacy matters. In a world where our digital footprints are constantly tracked, it’s crucial to safeguard our financial transactions and personal information from prying eyes. With Trezor Coinjoin, you can take back control.
What is Trezor Coinjoin? Trezor Coinjoin is an innovative feature offered by Trezor, the leading cryptocurrency hardware wallet provider. It allows you to combine your cryptocurrency transactions with other users, making it challenging for anyone to trace the origin or destination of your funds.
Enhance your anonymity. By participating in a Coinjoin transaction, your cryptocurrency activity becomes indistinguishable from others, effectively breaking the chain of transaction history and providing you with an added layer of privacy.
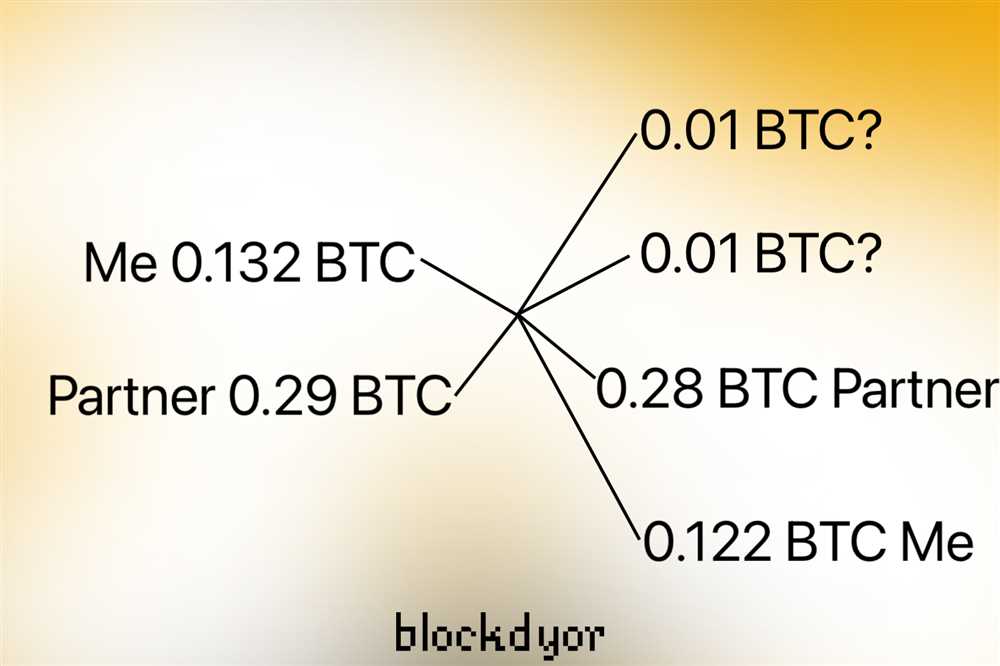
How does it work? Trezor Coinjoin utilizes a complex algorithm to mix your transactions with others, creating a massive pool of inputs and outputs. As a result, it becomes nearly impossible for anyone to determine which transaction belongs to whom.
Why choose Trezor Coinjoin?
- Unmatched security: Trezor Coinjoin leverages the highest security standards in the industry, ensuring that your transactions and private keys remain encrypted and protected.
- Seamless integration: Trezor Coinjoin seamlessly integrates with your Trezor hardware wallet, providing a user-friendly experience and making it easy for you to maintain your privacy and anonymity.
- Community-driven: With Trezor Coinjoin, you become part of a community committed to maintaining privacy in the cryptocurrency space. By collaborating with other users, you actively contribute to the overall strength and effectiveness of the Coinjoin feature.
Take control of your privacy today. Join thousands of satisfied users who have made Trezor Coinjoin their go-to solution for enhanced privacy and anonymity. Protect your digital assets and keep your financial transactions personal with Trezor Coinjoin.
The Importance of Privacy
Privacy is a fundamental right that every individual should have the ability to exercise. It allows people to protect their personal information and maintain control over their own lives. In today’s digital age, where data is constantly being collected and shared, the importance of privacy is more critical than ever before.
There are several reasons why privacy is important:
Protection from Identity Theft
When personal information is exposed, individuals become vulnerable to identity theft. This can lead to financial loss, reputational damage, and a loss of trust in online platforms. By prioritizing privacy, individuals can protect themselves from the risks associated with identity theft.
Preserving Personal Freedom
Privacy is essential for maintaining personal freedom. It allows individuals to express their thoughts and opinions without fear of repercussion or judgment. In a society where privacy is respected, people can fully exercise their rights to free speech, freedom of association, and freedom of expression.
Privacy promotes autonomy and individuality. It allows individuals to define their own identity and make choices without interference or surveillance. The ability to keep certain aspects of our lives private enables us to explore and express ourselves fully, without feeling judged or restricted.
Privacy also plays a significant role in fostering trust and building strong relationships. When individuals feel that their personal information is protected, they are more likely to engage in open and honest communication. This creates an environment where people feel safe to share their thoughts, ideas, and concerns.
Overall, privacy is an essential aspect of human dignity and personal freedom. It empowers individuals to control their personal information, safeguard their identities, and maintain their autonomy. In an increasingly interconnected world, where data is constantly being collected and analyzed, it is crucial that we prioritize and respect the importance of privacy.
Understanding the Risks
While Trezor Coinjoin offers enhanced privacy and anonymity, it is important to understand the potential risks involved in using this technology.
1. Counterparty Risks: When participating in a Coinjoin transaction, you are relying on other participants to follow the agreed-upon rules. There is a risk that some participants may act maliciously or attempt to deanonymize other participants.
2. Network Analysis Risks: While Coinjoin transactions provide a higher level of privacy, they are not completely immune to network analysis. Sophisticated analysis techniques can still be used to identify patterns or connections between participants, potentially compromising their privacy.
3. Regulatory Risks: Depending on your jurisdiction, using Coinjoin transactions may raise legal concerns. Some governments may view these transactions as attempts to evade regulations or engage in illicit activities. It is important to stay informed about the regulatory landscape and comply with the laws of your country.
4. Trust Risks: When using Trezor Coinjoin, you are placing trust in the developers and the technology itself. While the Trezor team has a solid reputation and the technology is built to be secure, there is always a risk of unforeseen vulnerabilities or exploits.
5. User Error Risks: Like any other technology, user error can compromise the effectiveness of Trezor Coinjoin. It is crucial to understand the instructions and use the technology correctly to ensure maximum privacy and anonymity.
By being aware of these risks and taking appropriate precautions, users can enjoy the benefits of Trezor Coinjoin while minimizing their exposure to potential vulnerabilities.
Protecting Your Information

When it comes to protecting your information and ensuring your privacy, there are several steps you can take. Here are some key measures you should consider:
1. Use Strong Passwords

One of the most basic yet important steps you can take to protect your information is to use strong passwords. Make sure your passwords are unique and not easily guessable. Avoid using personal information, such as your name or birthdate, in your passwords.
2. Enable Two-Factor Authentication
Two-factor authentication adds an extra layer of security to your accounts. It typically requires you to enter a verification code sent to your smartphone or another trusted device. Enable two-factor authentication whenever possible to prevent unauthorized access to your accounts.
3. Be Cautious of Phishing Attempts

Phishing is a technique used by hackers to trick you into revealing your personal information or login credentials. Be cautious of emails, messages, or websites that ask for sensitive information or prompt you to click on suspicious links. Always verify the sender’s identity and ensure the website’s URL is legitimate before entering any confidential information.
4. Update Your Software Regularly

Keeping your software up to date is crucial in protecting your information. Software updates often include security patches that address vulnerabilities and protect against known threats. Make sure you regularly update your operating system, web browsers, antivirus software, and other applications.
5. Use Encryption
Encryption converts your information into a secret code to keep it secure during transmission or storage. Use encryption tools and technologies whenever possible, such as SSL for secure website connections and end-to-end encryption for messaging apps. This helps safeguard your information from being intercepted by unauthorized individuals.
By following these steps and implementing strong security measures, you can significantly enhance the protection of your information and maintain your privacy.
The Role of Anonymity

When it comes to privacy and security in the digital world, anonymity plays a crucial role. Anonymity allows individuals to protect their personal information and activities from prying eyes, ensuring their privacy is preserved.
With the rise of cryptocurrencies and the increasing relevance of digital transactions, the need for anonymity has become even more important. Trezor Coinjoin is a solution that aims to enhance anonymity in the world of cryptocurrencies.
One of the key benefits of anonymity is the ability to transact without fear of your financial information being exposed to the public. By using the Trezor Coinjoin feature, users can mix their transactions with other participants, making it nearly impossible to trace the origin and destination of funds. This adds an extra layer of privacy and security to cryptocurrency transactions.
Anonymity also plays a significant role in protecting individuals from potential threats and unwanted attention. By keeping personal information anonymous, users can avoid becoming targets of hackers, scammers, or even government surveillance. This is particularly important in a world where personal data breaches and identity theft have become alarmingly common.
Furthermore, anonymity helps to secure the fungibility of cryptocurrencies. With fungibility, each unit of a cryptocurrency holds the same value as any other unit. However, without anonymity, certain units of a cryptocurrency might be tainted or associated with illegal activities, which could result in them being devalued or even rejected by merchants. Anonymity ensures that each unit of a cryptocurrency is indistinguishable from any other, guaranteeing its fungibility.
In conclusion, anonymity plays a vital role in protecting individuals’ privacy, securing their financial transactions, and preserving the fungibility of cryptocurrencies. The Trezor Coinjoin feature provides users with the means to achieve a higher level of anonymity, making it an essential tool for those looking to ensure their privacy and security in the digital world.
Anonymity in the Digital Age

In the digital age, where our lives are increasingly interconnected and our personal information is constantly being shared and tracked, anonymity has become a precious commodity. With each online transaction, social media post, and web search, we leave behind a digital trail that can be used to identify and track our every move.
The importance of anonymity cannot be overstated. It allows us to protect our privacy, maintain our personal security, and exercise our freedom of expression without fear of censorship or surveillance. Anonymity is especially vital for individuals living in repressive regimes or those who face discrimination or persecution based on their beliefs or identity.
The Threats to Anonymity

Unfortunately, anonymity in the digital age is constantly under threat. Governments, corporations, and malicious individuals are all eager to exploit our personal information for their own gain. From targeted advertising and data breaches to online surveillance and identity theft, the risks to our anonymity are numerous and ever-present.
One of the main challenges to anonymity is the pervasive collection and storage of personal data by tech companies. Our online activities are often tracked and monetized, leading to a loss of control over our own information. Additionally, advances in surveillance technologies and data analysis techniques make it easier than ever for organizations to identify and track individuals, even if they try to remain anonymous.
Protecting Your Anonymity
While maintaining complete anonymity online is nearly impossible, there are steps that individuals can take to protect their privacy and minimize their digital footprint. Utilizing tools such as virtual private networks (VPNs), encrypted messaging apps, and browsing in incognito mode can help safeguard your online activities.
It’s also important to be mindful of the information you share online and the permissions you grant to apps and websites. Limiting the personal data you provide and regularly reviewing your privacy settings can go a long way in preserving your anonymity.
Ultimately, protecting anonymity in the digital age requires a combination of technology, awareness, and advocacy. It’s crucial for individuals to stay informed about the latest threats to privacy and actively support efforts to strengthen legal protections for anonymity and data privacy.
Using Trezor Coinjoin
Trezor Coinjoin is a powerful tool that can enhance your privacy and anonymity when using cryptocurrencies. By utilizing the Coinjoin feature, you can mix your transactions with other users, making it difficult for anyone to trace the origins and destinations of your funds.
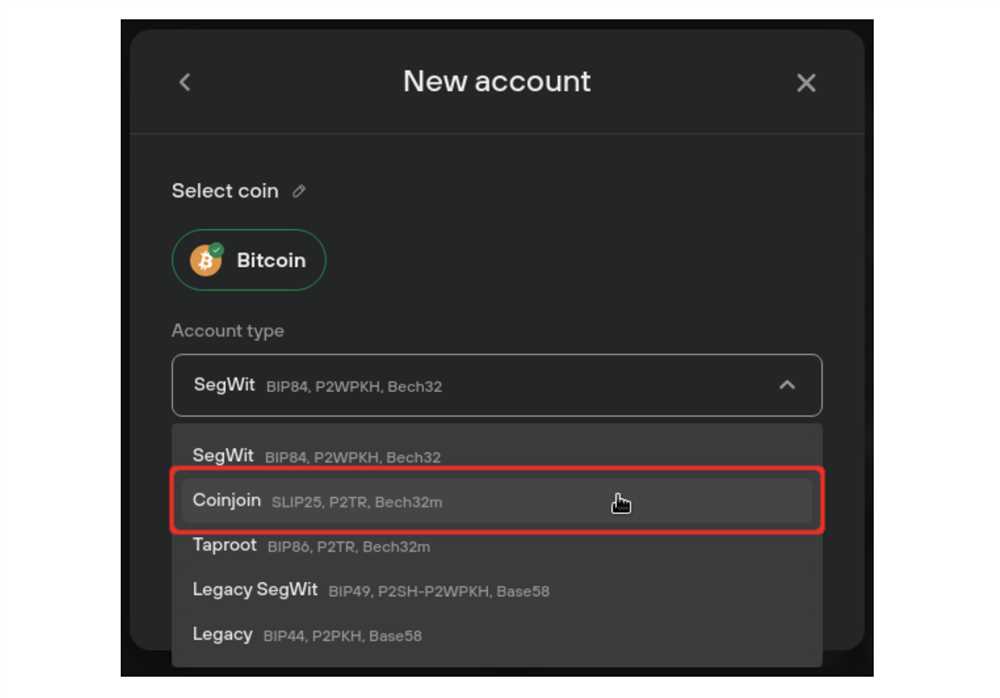
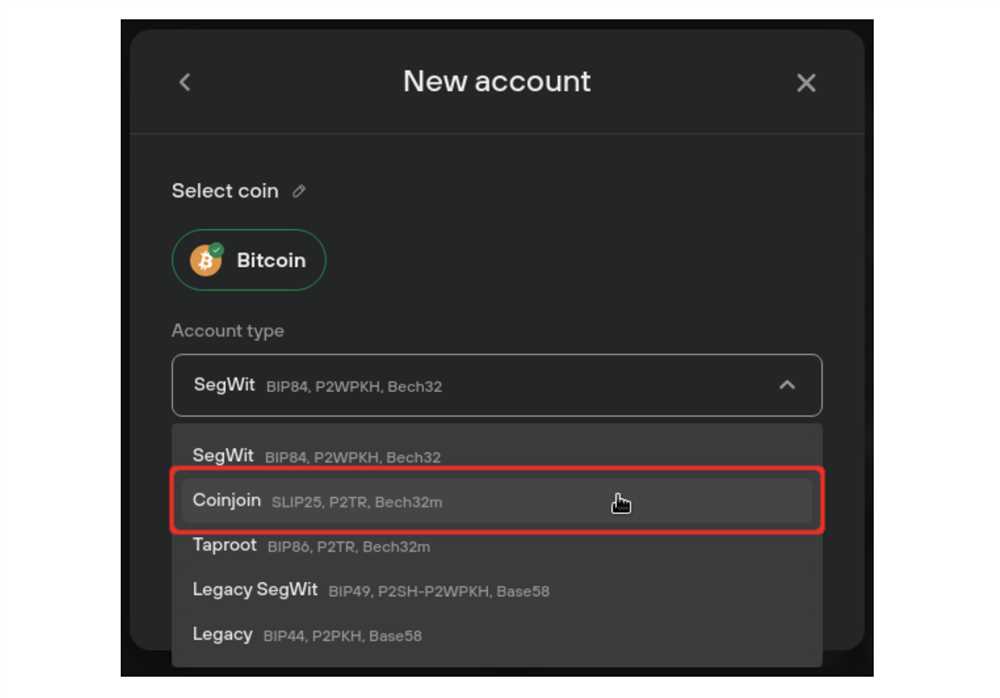
To use Trezor Coinjoin, you first need a Trezor hardware wallet. This wallet ensures that your private keys are stored securely offline, protecting you from potential online threats.
Once you have your Trezor wallet, you can enable the Coinjoin feature through the Trezor web interface. Simply connect your Trezor device to your computer, navigate to the Trezor web wallet, and follow the instructions to enable Coinjoin.
When you make a transaction using Trezor Coinjoin, your funds will be mixed with other users’ funds. This mixing process creates a high level of obfuscation, making it challenging for anyone to link your transaction to your identity.
It’s crucial to note that while Trezor Coinjoin enhances privacy, it does not provide complete anonymity. It is still essential to take other privacy measures, such as using Tor or VPNs, to further protect your identity.
Using Trezor Coinjoin not only adds an extra layer of privacy to your transactions but also helps promote a healthier and more fungible cryptocurrency ecosystem. By mixing your funds with others, you contribute to the collective effort of preserving the privacy and fungibility of cryptocurrencies.
In conclusion, Trezor Coinjoin is a valuable tool for anyone concerned about privacy and anonymity when using cryptocurrencies. By utilizing this feature, you can enhance the privacy of your transactions and contribute to the greater privacy and fungibility of cryptocurrencies as a whole.
Q&A:
What is “Understanding Privacy and Anonymity: Exploring Trezor Coinjoin” about?
“Understanding Privacy and Anonymity: Exploring Trezor Coinjoin” is a book that delves into the topic of privacy and anonymity in the context of cryptocurrency transactions. It specifically focuses on the concept of Coinjoin, which is a technique used to combine multiple transactions into a single transaction, making it harder to trace the original source of the funds.
Who is the author of “Understanding Privacy and Anonymity: Exploring Trezor Coinjoin”?
The author of “Understanding Privacy and Anonymity: Exploring Trezor Coinjoin” is a renowned cryptocurrency expert and privacy advocate. They have conducted extensive research on the topic and have a deep understanding of the underlying technology.
Why is privacy important in cryptocurrency transactions?
Privacy is important in cryptocurrency transactions for several reasons. Firstly, it helps protect the identity and financial information of the individuals involved in the transaction. It also enhances security by making it harder for malicious actors to track and target specific individuals. Additionally, privacy is crucial for maintaining fungibility, which ensures that all units of a cryptocurrency are interchangeable and hold the same value.
How does Trezor Coinjoin work?
Trezor Coinjoin works by combining multiple transactions from different individuals into a single transaction. This process involves mixing the inputs and outputs of the transactions, making it harder to trace the flow of funds. By participating in a Coinjoin transaction, individuals can enhance their privacy and anonymity in cryptocurrency transactions.


