
Trezor GitHub Enhancing Security for Open Source Projects

Open source projects have become an integral part of the tech community, allowing developers to collaborate, share ideas, and build upon each other’s work. However, this collaborative nature also poses security risks, as anyone can contribute code to these projects. To address this issue, Trezor, a leading provider of hardware wallets for cryptocurrencies, has taken the initiative to enhance security for open source projects on GitHub.
GitHub, the world’s largest platform for hosting and collaborating on open source projects, has been a breeding ground for malicious actors trying to exploit vulnerabilities in code. With millions of developers and repositories, it becomes challenging to ensure the security of every project. Trezor aims to change this by introducing new security features that add an extra layer of protection to open source projects on GitHub.
One of the key features introduced by Trezor is a code review system that scans every contribution made to a project on GitHub. This system automatically detects potentially malicious code, vulnerabilities, and common security flaws, allowing project maintainers to review and address them promptly. This helps in ensuring that only reliable and secure code makes its way into the project, reducing the risk of introducing vulnerabilities.
In addition to the code review system, Trezor also provides developers with a comprehensive security guide that outlines best practices for secure coding and project management. This guide covers topics such as secure authentication, data encryption, secure communication, and secure integration of external libraries. By following these guidelines, developers can make their projects more resilient to attacks and safeguard user data.
Trezor’s efforts to enhance security for open source projects on GitHub are commendable. By partnering with GitHub and providing tools and resources for secure coding, Trezor is not only making it easier for developers to create secure projects but also contributing to the overall security of the open source community. With these new security features in place, developers can collaborate with confidence, knowing that their projects are less vulnerable to malicious attacks.
Trezor GitHub Enhancing Security

In the world of open source projects, security is always a top concern. Trezor GitHub is taking steps to enhance security for its users by implementing various measures to protect against potential threats.
Commit Verification
One of the key security features of Trezor GitHub is commit verification. Every commit made by a developer is signed with their GPG key, ensuring that it has not been tampered with. This provides a layer of trust for users, as they can verify the authenticity of code changes.
Code Review Process
Another important aspect of enhancing security is the code review process. Trezor GitHub has a dedicated team of experienced developers who review every code change before it is merged into the main repository. This helps to identify any potential vulnerabilities or weaknesses in the code and ensures that only high-quality, secure code is included.
In addition to these measures, Trezor GitHub also encourages users to report any security vulnerabilities they may discover. This allows the team to quickly address any issues that arise and provide timely updates and patches to ensure the security of the project.
| Security Measures | Benefits |
|---|---|
| Commit Verification | Ensures code authenticity and integrity |
| Code Review Process | Identifies potential vulnerabilities and ensures high-quality code |
| Vulnerability Reporting | Promotes quick issue resolution and timely updates |
Open Source Advantages

Open source software offers a myriad of advantages that make it an attractive choice for developers and organizations alike.
1. Transparency and Trust

One of the key advantages of open source projects is the transparency it offers. The source code is openly available for everyone to inspect, which promotes trust and allows developers to ensure the security and reliability of the software. This level of transparency also enables a collaborative approach, where developers from all over the world can contribute to the project, leading to continuous improvements and innovation.
2. Cost Savings
Using open source software can significantly reduce costs for both individuals and organizations. Since the source code is open and freely available, there are no licensing fees to pay. This means that developers and organizations can save money that would otherwise be spent on purchasing proprietary software licenses. Additionally, open source software often has a vibrant community that offers support and assistance, reducing the need for expensive technical support services.
Furthermore, open source software can be customized and modified to fit specific needs without any restrictions, allowing developers and organizations to tailor the software to their exact requirements.
3. Security and Reliability
Open source software is often considered more secure and reliable than proprietary software. With the source code openly available, developers can identify and fix security vulnerabilities quickly. The collective effort of the community helps to identify and fix bugs faster, ensuring a more stable and reliable software ecosystem. Additionally, the transparency of open source projects allows for thorough audits and peer reviews, further enhancing security.
These advantages make open source software an increasingly popular choice for developers, contributing to the growth and success of the open source community.
Trezor GitHub Integration
As part of enhancing security for open-source projects, Trezor has introduced a seamless integration with GitHub. This integration allows developers to securely manage their repositories and access various features through their Trezor hardware wallets.
Features
The Trezor GitHub integration offers several important features that help protect your code and enhance the security of your open-source projects:
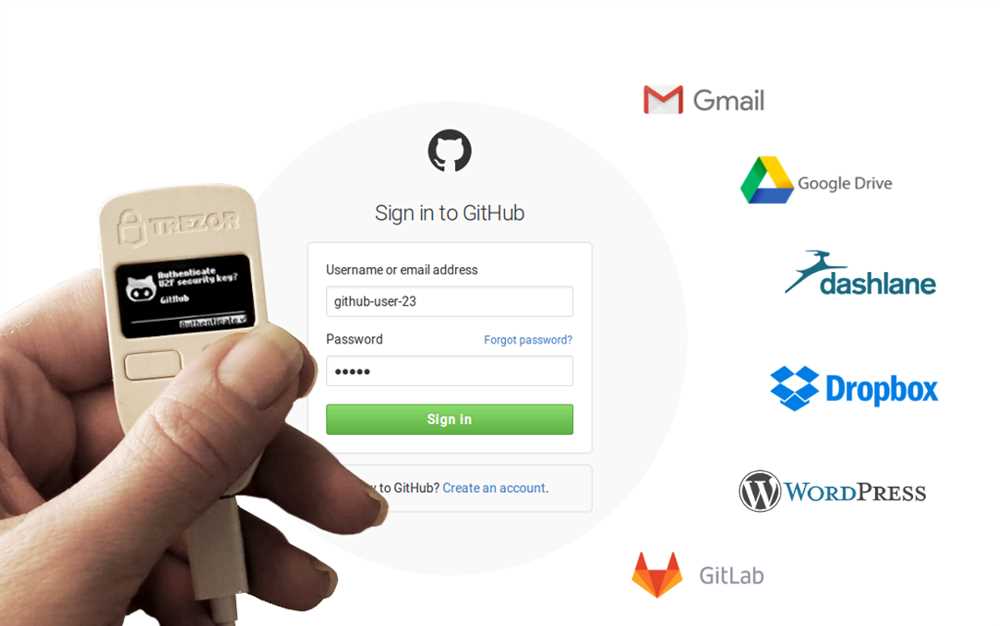
- Secure Repository Access: With Trezor hardware wallets, developers can securely authenticate and access their GitHub repositories, ensuring that only authorized individuals can make changes to the codebase.
- Two-Factor Authentication: Trezor provides an extra layer of security by integrating with GitHub’s two-factor authentication. This ensures that even if your GitHub account password is compromised, an attacker still cannot gain access to your repositories without the physical presence of the Trezor device.
- Transaction Signing: The integration enables developers to sign transactions related to their repositories using their Trezor hardware wallets. By verifying the transaction details on the device’s screen and confirming it with a physical button press, you can be confident that your code changes are secured.
Setup and Usage
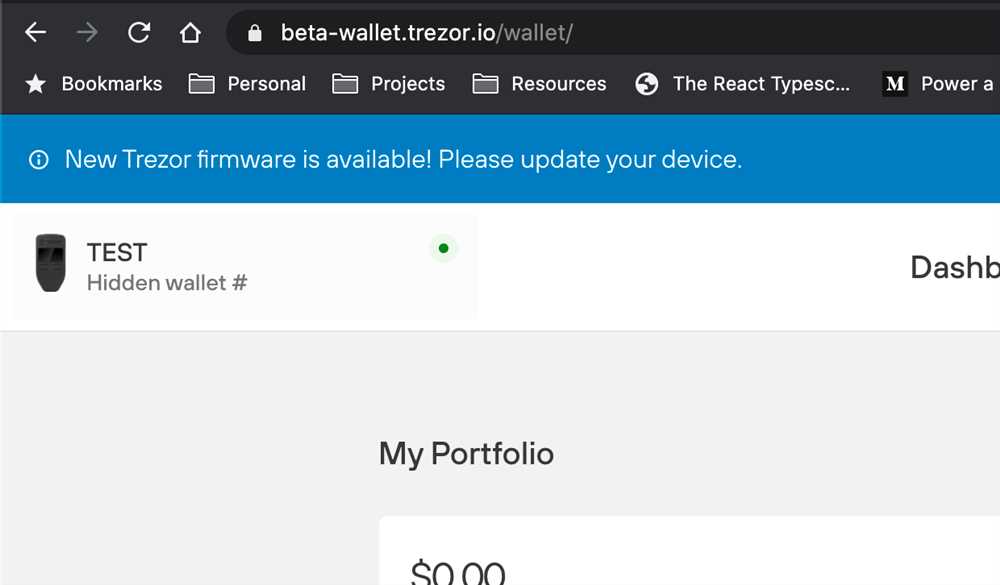
To start using the Trezor GitHub integration, follow these steps:
- Connect your Trezor hardware wallet to your computer.
- Navigate to the GitHub settings and select “Security & Privacy” from the sidebar.
- Click on “Manage third-party access” and locate the “Trezor” application.
- Click on the “Grant” button to authorize the Trezor application to access your repositories.
- Once the authorization is complete, you can use your Trezor hardware wallet to securely manage your GitHub repositories.
By integrating Trezor hardware wallets with GitHub, developers can enjoy enhanced security, protect their open-source projects, and have peace of mind knowing that their code changes are verified and secure.
| Benefits | Limitations |
|---|---|
|
|
Enhancing Security Measures
In order to enhance security for open source projects on Trezor GitHub, several measures can be implemented. These measures aim to protect the integrity and confidentiality of the codebase, as well as prevent unauthorized access and malicious activities.
1. Code Review Process
Implementing a robust code review process is essential to ensure the quality and security of the codebase. All changes to the code should be reviewed by multiple developers or trusted contributors before being merged. This process helps identify and fix any vulnerabilities or weaknesses in the code, reducing the risk of introducing security loopholes.
2. Vulnerability Scanning
Regular vulnerability scanning should be performed on the codebase to identify any potential security vulnerabilities. By using automated tools or services, developers can quickly detect common vulnerabilities such as known software bugs, insecure dependencies, or outdated libraries. These vulnerabilities can then be addressed promptly to prevent exploitation.
3. Secure Coding Practices
Adopting secure coding practices is crucial for developing secure open source projects. Developers should follow best practices such as input validation, output encoding, and proper error handling to minimize the risk of common security vulnerabilities like cross-site scripting (XSS) and SQL injection. Following secure coding guidelines and using secure coding libraries can significantly improve the overall security posture of the project.
4. Access Control

Limited access control should be implemented to ensure that only authorized individuals have access to the codebase. This can be achieved by using strong authentication mechanisms like two-factor authentication (2FA) and enforcing a least privilege principle. By limiting access to sensitive code, the risk of unauthorized modifications or leaks can be significantly reduced.
5. Security Audits

Periodic security audits should be conducted to assess the overall security of the open source project. These audits can be performed internally or by third-party security experts. The goal is to identify any potential security weaknesses, gaps in the security measures, or compliance issues. The findings from these audits can then be used to further enhance the security measures of the project.
| Measures | Description |
|---|---|
| Code Review Process | Multiple developers or trusted contributors review all code changes before merging. |
| Vulnerability Scanning | Regular scanning of the codebase to identify and address potential security vulnerabilities. |
| Secure Coding Practices | Follow secure coding guidelines to minimize common security vulnerabilities. |
| Access Control | Enforce limited access to the codebase with strong authentication mechanisms. |
| Security Audits | Periodic assessments of the overall security of the project to identify weaknesses. |
Benefits for Open Source Projects
Open source projects can greatly benefit from the security enhancements provided by Trezor GitHub. By implementing this solution, open source projects can ensure the integrity and authenticity of their codebase, preventing malicious actors from injecting vulnerabilities or compromising the project’s security.
Some of the key benefits for open source projects include:
| Improved Code Security | Trezor GitHub’s security features add an extra layer of protection to the codebase, making it more difficult for attackers to exploit vulnerabilities. |
|---|---|
| Enhanced Trust Among Contributors | By implementing strong security measures, open source projects can build trust and confidence among contributors, attracting more developers to contribute to the project. |
| Auditable and Transparent Codebase | The security features provided by Trezor GitHub ensure that the codebase remains auditable and transparent, allowing developers and security experts to review the code for any vulnerabilities. |
| Protection Against Code Injection | Trezor GitHub helps to protect against code injection attacks, preventing any unauthorized changes from being introduced into the codebase. |
| Secure Collaboration | With Trezor GitHub, open source projects can facilitate secure collaboration among developers, ensuring that only trusted individuals have access to the codebase. |
Overall, Trezor GitHub provides open source projects with an additional layer of security, helping to protect the codebase and build trust among contributors. By implementing these security enhancements, open source projects can create a more secure and reliable software ecosystem.
Question-answer:
What is Trezor GitHub?
Trezor GitHub is a platform that provides enhanced security for open source projects by offering a hardware wallet that stores cryptographic keys offline.
How does Trezor GitHub enhance security?
Trezor GitHub enhances security by keeping the cryptographic keys used in open source projects offline on a hardware wallet, preventing them from being compromised by online attacks.


