
Tips for Keeping Your Trezor Wallet Safe from Hackers

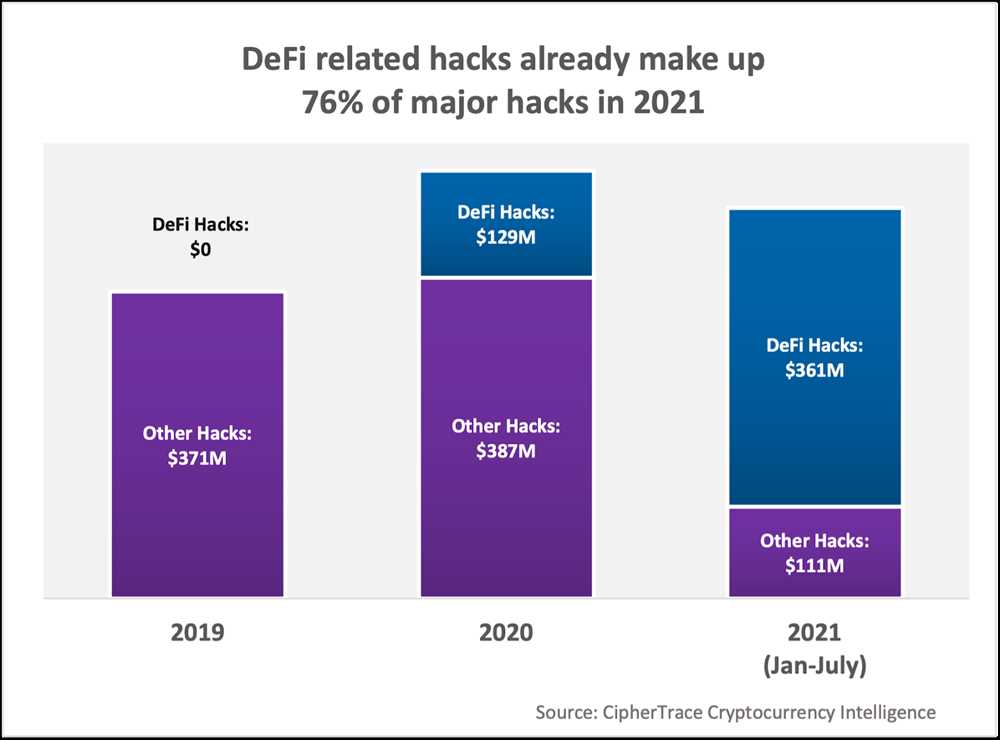
In the constantly evolving world of cryptocurrencies, security remains a top concern for investors and users alike. With the increasing popularity of digital currencies, hackers are constantly developing new ways to exploit vulnerabilities in wallet systems. Recently, there has been a surge in attacks targeting Trezor wallet users, one of the most popular and secure hardware wallets on the market.
Trezor wallets have gained a reputation for their excellent security features, such as offline storage and two-factor authentication. Despite this, hackers have found ways to compromise the wallets and gain unauthorized access to users’ funds. These attacks can range from phishing attempts to sophisticated malware designed to steal sensitive information.
So, how can Trezor wallet users stay safe from these attacks? Firstly, it is crucial to always be cautious and vigilant when interacting with any online platform or service related to your wallet. This includes being cautious of suspicious emails, links, and messages that ask for your private keys or personal information. Remember, Trezor or any other legitimate wallet provider will never ask for such sensitive information.
Secondly, keeping your firmware up to date is essential to maintain the security of your Trezor wallet. The developers behind Trezor regularly release firmware updates that include security patches and bug fixes. By regularly updating your firmware, you ensure that your wallet is protected against the latest known vulnerabilities.
Hackers Target Trezor Wallet Users
Maintaining the safety and security of your cryptocurrency investments is paramount in today’s digital landscape. Unfortunately, hackers are continuously finding new ways to target unsuspecting users, and recently they have set their sights on Trezor Wallet users.
Trezor Wallet is one of the most popular hardware wallets, known for its robust security features. However, even with its advanced protections, hackers are still attempting to exploit vulnerabilities and gain unauthorized access to users’ funds.
Phishing Attacks
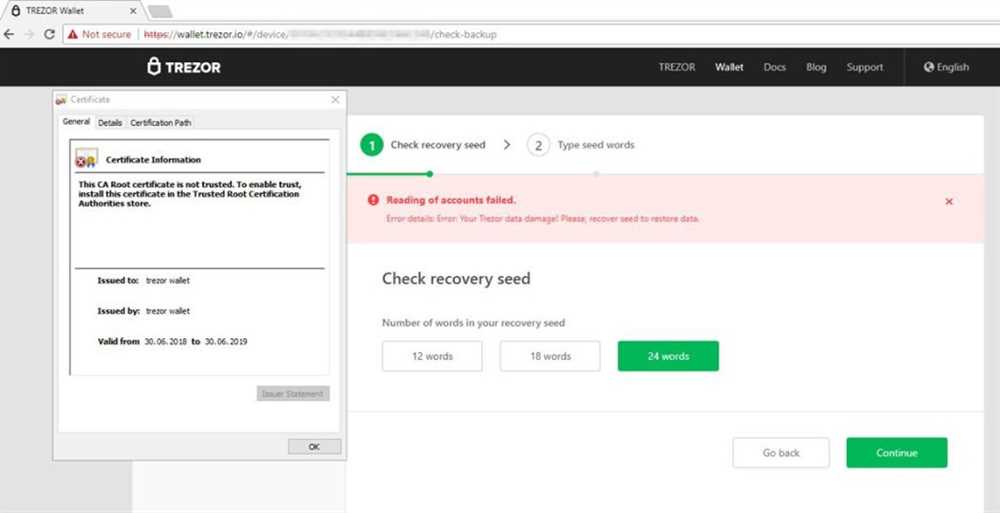
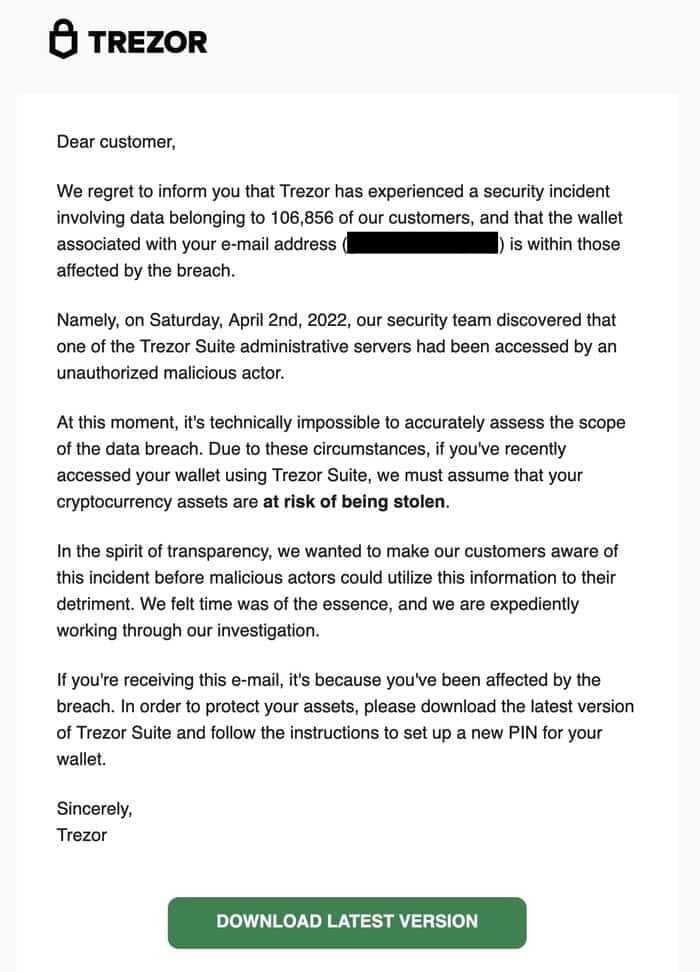
One common method employed by hackers to target Trezor Wallet users is through phishing attacks. These attacks involve sending deceptive emails or messages that appear to be from Trezor or other trusted sources. The goal is to trick unsuspecting users into providing sensitive information, such as their wallet’s recovery seed or private key.
To protect yourself from phishing attacks, always verify the legitimacy of any email or message before taking any action. Look for signs of suspicious grammar or spelling errors, and never click on any links from unrecognized sources.
Malware and Keyloggers

Another technique used by hackers is to infect users’ devices with malware or keyloggers. These malicious programs can record keystrokes or steal sensitive information, allowing hackers to gain access to your wallet.
To prevent malware and keyloggers, it is essential to use up-to-date antivirus software and regularly scan your devices for any potential threats. It is also advisable to avoid downloading files or software from untrusted sources.
Additionally, it is recommended to enable two-factor authentication (2FA) and utilize a strong and unique password for your Trezor Wallet.
Stay Informed and Be Vigilant

As the techniques of hackers continue to evolve, it is crucial to stay informed about the latest security risks and best practices. Follow reputable cryptocurrency and security websites, forums, and social media channels for the latest updates.
Remember, the safety of your cryptocurrency investments depends on your vigilance and adherence to proper security practices. By staying informed and taking proactive measures, you can reduce the risk of falling victim to hackers targeting Trezor Wallet users.
Ensure Your Security

As a Trezor wallet user, it is crucial to take steps to ensure the security of your digital assets. Follow these best practices to protect your funds from potential hacking attempts:
1. Keep Your Wallet Firmware Updated

Trezor regularly releases firmware updates to address any security vulnerabilities. Make sure to check for updates regularly and install them as soon as they become available. This will ensure that your wallet has the latest security patches.
2. Enable Passphrase and Two-Factor Authentication

Using a strong and unique passphrase for your Trezor wallet adds an extra layer of protection. Additionally, enabling two-factor authentication will require an extra verification step before accessing your wallet. This will make it significantly harder for hackers to gain access to your funds.
3. Be Mindful of Phishing Attempts

Hackers often use phishing techniques to trick users into revealing their wallet information. Always double-check the URL of the Trezor website before entering any sensitive information. Be cautious of any suspicious email or message requesting your wallet credentials and never share your recovery seed with anyone.
4. Secure Your Computer and Internet Connection
Ensure that your computer has up-to-date antivirus software installed and a firewall enabled to protect against malware and unauthorized access attempts. Avoid using public Wi-Fi networks when accessing your wallet and regularly monitor your network for any suspicious activities.
5. Use a Strong, Unique Password
Create a strong and unique password for your Trezor wallet. Avoid using common passwords or personal information that can be easily guessed. Consider using a password manager to securely store and generate complex passwords for all your online accounts.
Remember, the security of your Trezor wallet ultimately depends on your actions. By implementing these security measures, you can significantly reduce the risk of falling victim to hackers and keep your digital assets safe.
Protect Your Cryptocurrency
When it comes to storing your cryptocurrency, it’s crucial to prioritize security. With the rise in hacking attempts and thefts, taking the necessary precautions can help safeguard your digital assets. Follow these tips to protect your cryptocurrency:
1. Use a Hardware Wallet
Consider using a hardware wallet like Trezor to store your cryptocurrencies. Hardware wallets provide an extra layer of security by keeping your private keys offline, away from potential cyber threats. Make sure to purchase your wallet directly from the manufacturer and avoid buying second-hand devices to minimize the risk of tampering.
2. Enable Two-Factor Authentication
Enable two-factor authentication (2FA) for your cryptocurrency exchange accounts. This adds an extra step to the login process by requiring a unique verification code in addition to your password. Use an authenticator app or a hardware token for 2FA rather than relying on text messages, as they can be intercepted by hackers.
3. Protect Your Private Keys
Keep your private keys offline and secure. Consider writing them down on paper and storing them in a safe place, like a lockbox or a bank vault. Avoid storing your private keys in digital format, such as screenshots or cloud storage, as they can be vulnerable to hacking.
4. Beware of Phishing Attacks
Be cautious of phishing attacks, where hackers pose as legitimate websites or services to steal your login credentials. Always double-check the URL of the website before entering any sensitive information. Avoid clicking on suspicious links or downloading files from unknown sources, as they could contain malware.
5. Regularly Update Your Software
Keep your cryptocurrency wallets and any related software up to date. Developers often release updates that include bug fixes and security enhancements. Regularly check for updates and apply them promptly to ensure you have the latest protection against potential vulnerabilities.
6. Use Strong Passwords

Create strong and unique passwords for all your cryptocurrency accounts. Avoid using easily guessed passwords or reusing the same password across multiple platforms. Consider using a password manager to securely store your passwords and generate complex ones.
| Do: | Don’t: |
|---|---|
| Use a hardware wallet to store your cryptocurrency | Store your private keys in a digital format |
| Enable two-factor authentication for your exchange accounts | Click on suspicious links or download files from unknown sources |
| Protect your private keys offline | Use easily guessed passwords |
| Stay vigilant against phishing attacks | Use second-hand hardware wallets |
| Regularly update your software | Reuse the same password across multiple platforms |
Stay One Step Ahead of Hackers
To protect your Trezor wallet from hackers, it is important to stay vigilant and employ the necessary security measures. Here are some tips to help you stay one step ahead:
1. Keep your software up to date
Regularly update your Trezor wallet’s software to ensure that you have the latest security patches. This will help protect you from any known vulnerabilities that hackers may target.
2. Use a strong passphrase
In addition to your PIN, consider adding a strong passphrase to your Trezor wallet. This adds an extra layer of security and makes it more difficult for hackers to gain access to your funds.
3. Be cautious of phishing attempts
Hackers often use phishing emails or websites to trick users into revealing their wallet credentials. Be cautious of any emails or links that ask for your wallet information and always verify their legitimacy before providing any sensitive information.
4. Avoid public Wi-Fi networks: When accessing your Trezor wallet, avoid using public Wi-Fi networks as they may not be secure. Instead, use a trusted and secure internet connection to ensure that your transactions are safe.
5. Regularly check for suspicious activity: Regularly check your Trezor wallet for any unauthorized transactions or suspicious activity. If you notice anything unusual, take immediate action to secure your funds and report it to the appropriate authorities.
By following these tips, you can stay one step ahead of hackers and keep your Trezor wallet and funds secure.
Q&A:
What is Trezor Wallet?
Trezor Wallet is a hardware cryptocurrency wallet that stores private keys offline, providing a high level of security for digital assets.
How do hackers target Trezor Wallet users?
Hackers can target Trezor Wallet users through various means such as phishing emails, fake software updates, or compromised websites that mimic the official Trezor website.
What can users do to stay safe from hackers?
Users can stay safe from hackers by being cautious of phishing attempts, only downloading software updates from the official Trezor website, and regularly checking their Trezor Wallet for any unusual activity.
Are there any signs that my Trezor Wallet may have been compromised?
Some signs that your Trezor Wallet may have been compromised include unexpected transactions, a different balance than expected, or the device behaving unexpectedly.
What should I do if I suspect my Trezor Wallet has been compromised?
If you suspect your Trezor Wallet has been compromised, you should immediately disconnect it from your computer, contact Trezor support for assistance, and consider transferring your funds to a new wallet.


