
The Security Features of Trezor One: Staying Ahead of Threats

In today’s digital age, securing your cryptocurrency assets is of utmost importance. With the rise in hacking incidents and cyber threats, it is crucial to choose a hardware wallet that can provide robust security measures. One such popular option is the Trezor One, a hardware wallet that has gained a significant reputation in the crypto community.
But how effective are the security features of Trezor One in keeping up with the ever-evolving threats? With new vulnerabilities and attack vectors emerging constantly, it is essential to evaluate whether this hardware wallet can withstand the sophisticated techniques employed by malicious actors.
Trezor One, developed by SatoshiLabs, is known for its focus on security and user privacy. It combines the convenience of a hot wallet with the security of a cold wallet, offering a seamless user experience while safeguarding your digital assets.
One of the key features of Trezor One is its offline storage capability. The private keys, which are essential for accessing and managing your cryptocurrencies, are generated and stored securely on the device itself. This ensures that your keys are never exposed to the internet, making it much harder for hackers to gain unauthorized access to your funds.
Evaluating the Current Security Measures

Ensuring the security of our digital assets is of utmost importance when using a hardware wallet like Trezor One. In this section, we will evaluate the current security measures provided by Trezor One and assess their effectiveness in keeping up with the ever-evolving threats in the cryptocurrency space.
Secure Element Integration
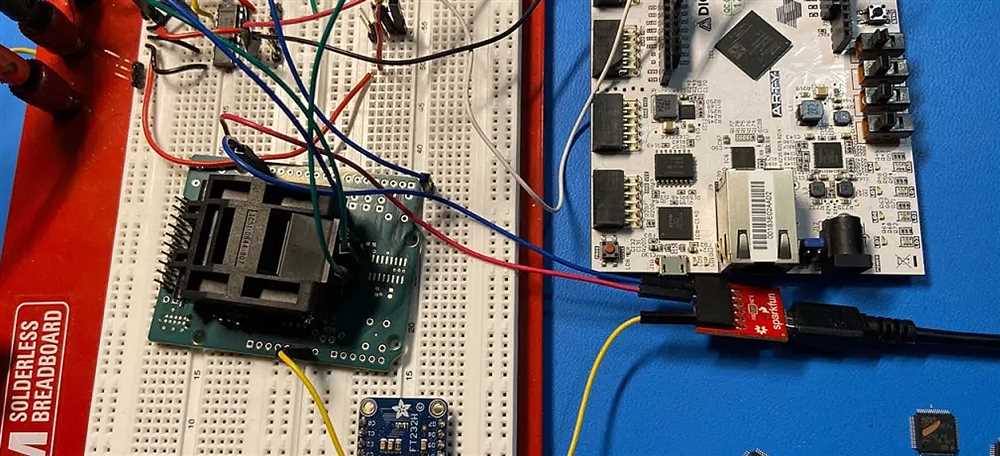
Trezor One incorporates a secure element chip in its design, which provides an extra layer of security to protect the private keys. The secure element is a tamper-proof chip that stores the private keys securely and performs cryptographic operations. This separation of sensitive information from the main microcontroller enhances the resistance against physical and software attacks.
Offline Storage of Private Keys

Trezor One ensures offline storage of private keys, meaning that the private keys never leave the device. This significantly reduces the risk of being compromised by malware or hackers. By keeping the private keys offline, Trezor One eliminates the potential attack vectors associated with online wallets or software-based wallets.
Passphrase Encryption
Trezor One allows users to set up a passphrase for additional security. This passphrase acts as an extra layer of encryption for the device, making it even more challenging for unauthorized individuals to access the funds. By encrypting the passphrase and keeping it separate from the device, the security is further enhanced.
Firmware Integrity Checks

Trezor One employs a robust firmware integrity check mechanism, ensuring that the device only runs firmware that has been signed and verified by the manufacturer. This prevents any tampering with the firmware and protects against malicious updates. By regularly verifying the integrity of the firmware, users can have confidence in the security of their device.
Strong PIN Protection

The PIN protection feature helps prevent unauthorized access to the device in case of physical theft or loss. Trezor One enforces a limited number of attempts for entering the correct PIN, making it difficult for attackers to guess the PIN through brute force attacks. Additionally, the device wipes itself clean after a specified number of unsuccessful attempts, further safeguarding the private keys.
| Security Measure | Effectiveness |
|---|---|
| Secure Element Integration | High |
| Offline Storage of Private Keys | High |
| Passphrase Encryption | Medium |
| Firmware Integrity Checks | High |
| Strong PIN Protection | High |
Overall, Trezor One’s current security measures are considered to be highly effective in protecting the private keys and safeguarding against various threats. While there is always room for improvement, Trezor One has demonstrated a commitment to staying ahead of the evolving security landscape.
Assessing the Vulnerabilities and Potential Risks

The Trezor One wallet, while offering a high level of security, is not immune to vulnerabilities and potential risks. It is important for users to be aware of these factors to ensure the safety and security of their cryptocurrency holdings.
One potential vulnerability is physical theft of the device. Although the Trezor One is designed to be tamper-resistant and hardened against physical attacks, it is still possible for someone to steal the device and gain access to the wallet’s private keys. To mitigate this risk, it is important to store the device in a secure location and consider enabling additional security measures such as a PIN or passphrase.
Another potential risk is the compromise of the device’s security through malware or phishing attacks. While the Trezor One has built-in measures to protect against these risks, it is still crucial for users to exercise caution when interacting with their wallet. This includes being vigilant about the sources of software updates, carefully verifying transaction details, and avoiding entering sensitive information on potentially compromised devices.
There is also the risk of software vulnerabilities that could potentially be exploited by attackers. The Trezor One team regularly releases firmware updates to address known vulnerabilities and improve the security of the device. It is important for users to stay up to date with these updates and promptly install them to ensure the most robust level of security.
Additionally, it is worth considering the risk of human error. It is possible for users to accidentally reveal sensitive information, such as their recovery seed, to unauthorized individuals. It is imperative to follow best practices for handling the wallet, including securely storing the recovery seed and practicing caution when providing any information related to the wallet.
To summarize, while the Trezor One offers a high level of security, there are still potential vulnerabilities and risks that users should be aware of. It is crucial to implement best practices and stay informed about potential threats in order to safeguard one’s cryptocurrency holdings.
| Vulnerability | Potential Risk |
|---|---|
| Physical theft of the device | Gaining access to the wallet’s private keys |
| Compromise of security through malware or phishing attacks | Possible theft of sensitive information |
| Software vulnerabilities | Potential exploitation by attackers |
| Human error | Accidentally revealing sensitive information |
Exploring the Latest Upgrades and Updates
Trezor One, a popular hardware wallet, has continuously evolved to stay ahead of the ever-evolving threats in the crypto space. In this section, we will explore the latest upgrades and updates that Trezor One has implemented to ensure the highest level of security for its users.
One of the most significant upgrades is the introduction of passphrase encryption. With this feature, users can add an additional layer of protection to their funds by creating a unique passphrase that is required to access the wallet. This ensures that even if the device is lost or stolen, the funds remain secure.
Another important update is the implementation of Shamir Backup, a multi-signature solution. This feature allows users to split their recovery seed into multiple parts, known as shares. These shares can be distributed among trusted individuals, ensuring that no single person can gain access to the entire seed. Shamir Backup significantly reduces the risk of physical attacks on the device.
Trezor One has also introduced a feature called “MicroSD card support.” This allows users to encrypt and back up their recovery seed on a MicroSD card, which can then be stored in a secure location. By keeping the seed offline, users can protect it from potential online attacks.
In addition to these security-focused upgrades, Trezor One has also made improvements to its firmware and user interface. The firmware updates are designed to address any potential vulnerabilities and ensure the device’s overall performance and stability. The user interface updates aim to enhance the overall user experience and make navigating through the device’s features more intuitive.
Furthermore, Trezor One continues to work closely with security researchers and community members to identify and address any potential vulnerabilities. Regular bug bounty programs are conducted to incentivize and reward individuals who discover and report security issues. This collaborative approach ensures that the device’s security features stay up to date and can withstand emerging threats.
| Upgrade/Update | Description |
|---|---|
| Passphrase Encryption | Adds an extra layer of security by requiring a unique passphrase to access the wallet. |
| Shamir Backup | Allows users to split their recovery seed into multiple shares, reducing the risk of physical attacks on the device. |
| MicroSD Card Support | Enables users to encrypt and back up their recovery seed on a MicroSD card for offline storage. |
| Firmware Updates | Regular updates to address vulnerabilities and improve performance and stability. |
| User Interface Updates | Enhancements to the device’s interface to improve user experience and ease of use. |
In conclusion, Trezor One has made significant upgrades and updates to its security features to keep up with the evolving threats in the crypto space. These enhancements, such as passphrase encryption, Shamir Backup, and MicroSD card support, provide users with added protection and peace of mind. By continually improving its firmware and user interface, Trezor One ensures that its users have a secure and user-friendly experience.
Future-proofing Trezor One’s Security

In order to stay ahead of the evolving threats in the digital landscape, it is essential to continually update and enhance the security features of Trezor One. By future-proofing its security, Trezor One can ensure that it remains a reliable and secure hardware wallet for years to come.
1. Introducing Advanced Encryption Technology
One way to future-proof the security of Trezor One is to adopt advanced encryption technology. This includes implementing stronger encryption algorithms and key management systems to protect the user’s private keys and sensitive information. By staying ahead of potential advancements in hacking techniques, Trezor One can provide a higher level of security and peace of mind to its users.
2. Regular Firmware Updates

Another important aspect of future-proofing Trezor One’s security is to regularly release firmware updates. These updates should not only address any identified security vulnerabilities but also incorporate new features and improvements. By keeping the firmware up-to-date, Trezor One can ensure that it adapts to emerging threats and remains a trustworthy solution for storing digital assets.
It is crucial for the Trezor team to maintain a proactive approach by continuously monitoring and assessing potential security risks. By doing so, they can respond quickly to any new threats and implement necessary changes to safeguard the assets of Trezor One users.
In conclusion, future-proofing the security of Trezor One is essential in order to maintain its reputation as a reliable hardware wallet. By incorporating advanced encryption technology and regularly updating the firmware, Trezor One can continue to provide a secure storage solution for digital assets.
Q&A:
What are the security features of Trezor One?
Trezor One has several security features including a PIN code, a recovery seed, and a password manager. These features help protect your cryptocurrencies from unauthorized access.
How does the PIN code work on Trezor One?
The PIN code on Trezor One is a 4-8 digit number that acts as the first line of defense against unauthorized access. It needs to be entered correctly in order to unlock the device and access your cryptocurrencies.
What is a recovery seed in Trezor One?
A recovery seed is a set of 24 words that is generated during the initial setup of Trezor One. It serves as a backup in case your device is lost, stolen, or damaged. You can use the recovery seed to restore your wallet and access your cryptocurrencies.
Does Trezor One have a password manager?
Yes, Trezor One has a password manager feature called “Passwords” that can securely store and manage your passwords. It encrypts your passwords with your device’s PIN code and protects them from unauthorized access.


