
Protecting Your Investments: Evaluating the Security of Popular Hardware Wallets After the Trezor Breach

In recent years, the use of hardware wallets has gained significant popularity among cryptocurrency enthusiasts as a secure solution for storing digital assets. These devices offer an extra layer of protection by keeping private keys offline and out of reach from potential hackers and malware. However, a recent incident involving the Trezor hardware wallet has raised concerns about the overall security of such devices.
The breach, which occurred in a Trezor wallet manufacturing plant, has highlighted the vulnerability of hardware wallets to physical attacks. In this particular case, a malicious insider gained unauthorized access to the plant and tampered with a batch of wallets before they were shipped to customers. This incident serves as a wake-up call for the cryptocurrency community, urging them to reevaluate the security measures of hardware wallets.
While it is crucial to note that the breach was an isolated incident and the vast majority of hardware wallets remain secure, it has raised questions about the potential risks associated with these devices. It emphasizes the need for manufacturers to implement stringent security protocols throughout the entire production process to minimize the risk of tampering.
As users, it is imperative to stay informed about the security features offered by hardware wallet manufacturers. Factors such as the choice of secure elements, firmware updates, encryption, and multi-factor authentication should be carefully considered when selecting a hardware wallet. Additionally, users should also be vigilant and regularly check for any suspicious activities or signs of device tampering.
In conclusion, the recent breach involving the Trezor hardware wallet has prompted a necessary evaluation of the security measures implemented by hardware wallet manufacturers. The incident serves as a reminder that even the most robust security systems can still be vulnerable to physical attacks. Therefore, it is crucial for both manufacturers and users to constantly reassess and enhance the security protocols to safeguard the digital assets of cryptocurrency enthusiasts.
Evaluating Hardware Wallet Security

Hardware wallets are designed to securely store cryptocurrency assets, providing an additional layer of protection compared to software wallets. However, recent events, such as the Trezor breach, have raised concerns about the security of these devices. This article aims to evaluate the security of hardware wallets, taking into account various factors that can impact their overall level of protection.
One of the key aspects to consider when evaluating hardware wallet security is the physical design and construction of the device. A well-designed hardware wallet should have robust tamper resistance features, such as hardened materials and secure enclosures, to prevent physical attacks. Additionally, the device should have reliable firmware that is regularly updated to address any security vulnerabilities.
Another important factor is the cryptographic mechanisms used by the hardware wallet. It should employ strong encryption algorithms and key management techniques to protect the private keys stored on the device. The wallet should also provide a secure way to generate and store recovery phrases, which are used for wallet backup and restoration.
The software used to interact with the hardware wallet is another critical element to evaluate. It should have a clean and intuitive user interface, making it easy for users to securely manage their cryptocurrency assets. The software should also implement proper authentication mechanisms, such as two-factor authentication, to prevent unauthorized access to the wallet.
| Factor | Evaluation |
|---|---|
| Physical Design | The hardware wallet should have robust tamper resistance features and secure enclosures. |
| Cryptographic Mechanisms | The wallet should employ strong encryption algorithms and secure key management techniques. |
| Software Interface | The software should have a clean and intuitive user interface and implement proper authentication mechanisms. |
Furthermore, the manufacturer’s reputation and track record should also be evaluated. A reputable manufacturer would have a history of promptly addressing security flaws and providing regular firmware updates to enhance the wallet’s security. It is also important to check for any independent security audits or certifications that the hardware wallet has undergone.
Lastly, user behavior and best practices play a significant role in hardware wallet security. Users should follow guidelines provided by the manufacturer, such as enabling PIN protection, using strong and unique passwords, and keeping the recovery phrases offline and secure.
In conclusion, evaluating hardware wallet security requires considering various factors such as physical design, cryptographic mechanisms, software interface, manufacturer reputation, and user behavior. By carefully examining these aspects, users can make informed decisions when selecting a hardware wallet and take appropriate measures to safeguard their cryptocurrency assets.
Trezor Breach and its Impact

The discovery of the breach in Trezor, a popular hardware wallet, sent shockwaves through the cryptocurrency community. This incident raised serious concerns regarding the security of hardware wallets and the potential vulnerability of users’ funds.
Trezor is a well-known and trusted brand in the crypto space. The breach, which occurred due to a flaw in the device’s firmware, revealed that even the most reputable and established products in the industry can have vulnerabilities.
The impact of the Trezor breach was significant. It not only eroded the trust that users had in the security of their hardware wallets, but it also highlighted the need for better security practices within the industry.
Many users who had stored their cryptocurrencies in Trezor wallets were left feeling exposed and vulnerable. The breach served as a wakeup call for them to reassess their security measures and take additional precautions to protect their funds.
The Trezor breach also had repercussions on the reputation of the company. Trezor had to work tirelessly to regain the trust of its customers and address the security concerns raised by the incident. This incident underscored the importance of timely disclosure of breaches and transparent communication with the affected users.
The incident also had wider implications for the entire hardware wallet industry. It highlighted the need for rigorous security testing and regular firmware updates to enhance the resistance of hardware wallets to potential attacks.
In conclusion, the Trezor breach had a profound impact on both individuals and the hardware wallet industry as a whole. It exposed vulnerabilities in a widely respected product and served as a wake-up call for users to prioritize their own security measures. The incident also emphasized the importance of timely disclosure and transparency within the industry to maintain trust and confidence in hardware wallets.
Key Factors in Evaluating Hardware Wallet Security
When evaluating the security of a hardware wallet, it is important to consider several key factors. These factors can help determine the overall safety and reliability of the wallet, as well as its susceptibility to potential breaches or attacks.
- Secure Element: One of the most crucial aspects of a hardware wallet is the presence of a secure element. This hardware component provides an isolated and encrypted environment where private keys are stored and transactions are signed. A robust secure element is essential in preventing unauthorized access to sensitive data.
- Open Source: The openness of the hardware wallet’s software is another crucial factor. Open-source wallets allow anyone to review the code, identify vulnerabilities, and propose improvements. This transparency fosters trust and ensures that security flaws are quickly addressed and resolved.
- Code Audits: Regular code audits by reputable third-party security firms are essential to verify the integrity and security of a hardware wallet. These audits help in identifying any potential vulnerabilities or weaknesses that may have been overlooked during development and testing.
- Backup and Recovery: A reliable hardware wallet should provide users with a seamless backup and recovery process. This ensures that even in the event of loss, theft, or damage, users can safely recover their funds and access their accounts without compromising security.
- Multifactor Authentication: Implementing multiple layers of authentication adds an extra level of security to a hardware wallet. This could include PIN codes, passphrase encryption, or biometric authentication. These additional security measures help protect against unauthorized access.
- Secure Firmware Updates: Regular firmware updates are crucial for maintaining the security of a hardware wallet. However, these updates must be delivered securely and verified to prevent tampering or installation of malicious software. Hardware wallets should offer a secure update process to ensure the integrity of the device’s firmware.
- Strong Community and Support: A strong and active community, along with prompt support from the hardware wallet manufacturer, is important for addressing security concerns and resolving any issues that may arise. Regular communication and updates help to maintain user trust and confidence.
By considering these key factors and evaluating a hardware wallet’s security features, users can make informed decisions about which wallet best meets their needs and provides the highest level of security for their digital assets.
Recommendations for Ensuring Secure Cryptocurrency Storage

1. Invest in a reputable hardware wallet:
Choosing a reputable and well-established hardware wallet is essential to ensure secure cryptocurrency storage. Look for devices that have been thoroughly tested and audited for potential vulnerabilities. Additionally, consider opting for wallets that have a proven track record of implementing regular security updates and patches.
2. Enable two-factor authentication (2FA):
Utilizing two-factor authentication adds an extra layer of security to your cryptocurrency storage. By requiring a secondary verification method, such as a random generated code or fingerprint, it becomes significantly more difficult for unauthorized individuals to access your funds.
3. Keep software up to date:
Regularly updating your hardware wallet’s software is crucial to patching potential vulnerabilities and protecting against any new threats. Manufacturers often release updates that address security concerns, so it’s important to stay vigilant and apply these updates as soon as they become available.
4. Implement a strong PIN:
Setting a strong PIN for your hardware wallet provides an additional layer of protection against unauthorized access. Avoid using easily guessable combinations, such as birthdays or sequential numbers. Instead, opt for a longer PIN that contains a mix of numbers and letters.
5. Backup your recovery seed:
When setting up a new hardware wallet, you are often given a recovery seed – a series of words that can be used to restore access to your funds in case of loss or theft of the device. It is crucial to securely backup this recovery seed and store it offline in a safe place, separate from the hardware wallet itself.
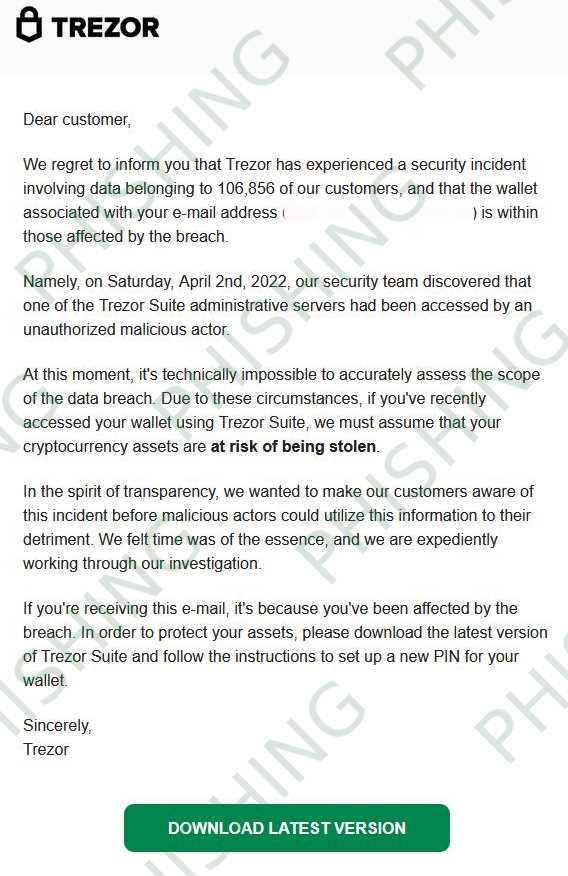
6. Be cautious of phishing attempts:
Cryptocurrency scams and phishing attempts are prevalent. Be wary of any communications or websites that request your hardware wallet’s information or recovery seed. Always verify the authenticity of the source before providing any sensitive information.
7. Consider using a multi-signature account:
A multi-signature account requires multiple signatures to authorize transactions, providing an extra layer of security. By distributing control among multiple parties, the risk of a single point of failure is minimized.
8. Secure your physical device:
Ensure the physical security of your hardware wallet by keeping it in a safe and secure location when not in use. Avoid leaving it unattended or in areas with a higher risk of theft or damage.
9. Periodically review your transactions:
Regularly monitoring your cryptocurrency transactions can help identify any unusual or suspicious activity. If you notice any unauthorized transactions, immediately take steps to secure your funds and report the incident to the relevant authorities.
10. Stay updated on security best practices:
As the cryptocurrency landscape evolves, so do the security risks and best practices. Stay informed about the latest security recommendations and follow industry best practices to ensure your cryptocurrency storage remains secure.
Q&A:
What is the Trezor Breach?
The Trezor Breach refers to the security incident where hackers were able to access sensitive information from Trezor hardware wallets, compromising the security of the devices and potentially putting user funds at risk.
How did the hackers gain access to the Trezor wallets?
The exact method used by the hackers to gain access to the Trezor wallets is not yet known. However, it is believed that the hackers exploited a vulnerability in the firmware of the devices, allowing them to extract sensitive information.
Were any user funds stolen during the Trezor Breach?
At this time, it is not clear if any user funds were stolen as a result of the Trezor Breach. Trezor has stated that they have found no evidence of funds being moved or stolen, but they are urging users to take precautions and to consider their assets at risk.
What steps is Trezor taking to improve the security of their hardware wallets?
Trezor has acknowledged the breach and is taking steps to improve the security of their hardware wallets. They have released a firmware update that addresses the vulnerability used by the hackers and are advising users to update their devices as soon as possible. Additionally, Trezor is conducting a full security audit of their systems and implementing additional measures to enhance the security of their devices.


