
Understanding the Potential Threats to Trezor

In recent years, the rise of cryptocurrencies has brought with it a new wave of innovative solutions for storing and securing digital assets. One such solution is Trezor, a hardware wallet that offers users a secure and convenient way to store their cryptocurrencies offline. While Trezor is undoubtedly a powerful tool for protecting digital investments, it is important for users to be aware of the potential threats that exist in the ever-evolving landscape of cyberspace.
One of the most significant threats to Trezor is the risk of hacking. Cybercriminals are constantly devising new techniques to gain unauthorized access to digital wallets, and hardware wallets like Trezor are no exception. Hacking attempts can range from sophisticated phishing attacks to malware-infected devices that can compromise the security of Trezor’s private keys. It is crucial for users to remain vigilant and take proactive measures to protect their Trezor wallets from such attacks.
Another potential threat to Trezor is the risk of physical theft. Despite its robust security features, a hardware wallet like Trezor is still a physical object that can be stolen or lost. Whether it’s due to a burglary, a misplaced device, or an accident, the loss of a Trezor wallet can have devastating consequences for the owner. It is essential for users to keep their Trezor wallets in a secure location and regularly back up their private keys in case of unforeseen events.
Furthermore, it is crucial for users to be aware of the potential for social engineering attacks. Cybercriminals may attempt to exploit human psychology and manipulate individuals into disclosing sensitive information or granting access to their Trezor wallets. These attacks can take various forms, such as impersonating customer support representatives or sending phishing emails that appear to be from legitimate sources. Vigilance and skepticism are key in protecting oneself from falling victim to such social engineering attacks.
In conclusion, while Trezor offers robust security for storing cryptocurrencies, it is important for users to understand and mitigate the potential threats that exist. By remaining vigilant against hacking attempts, safeguarding against physical theft, and being aware of social engineering attacks, users can ensure the long-term security of their Trezor wallets and enjoy the benefits of a secure and convenient method for storing digital assets.
The Importance of Trezor Security

Trezor is a popular hardware wallet that offers a secure way to store cryptocurrencies. The security of Trezor is of utmost importance due to the potential threats that exist in the cryptocurrency world.
One of the key features of Trezor is its use of advanced encryption algorithms to protect the private keys that are used to access and transfer cryptocurrencies. These encryption algorithms ensure that even if a hacker manages to gain physical access to the device, they would still need to crack the encryption to access the private keys.
In addition to encryption, Trezor also implements multiple layers of security protocols to further protect the device. These include a PIN code that is required to access the device, a passphrase that adds an extra layer of security, and a recovery seed that allows users to restore their funds in case the device is lost or stolen.
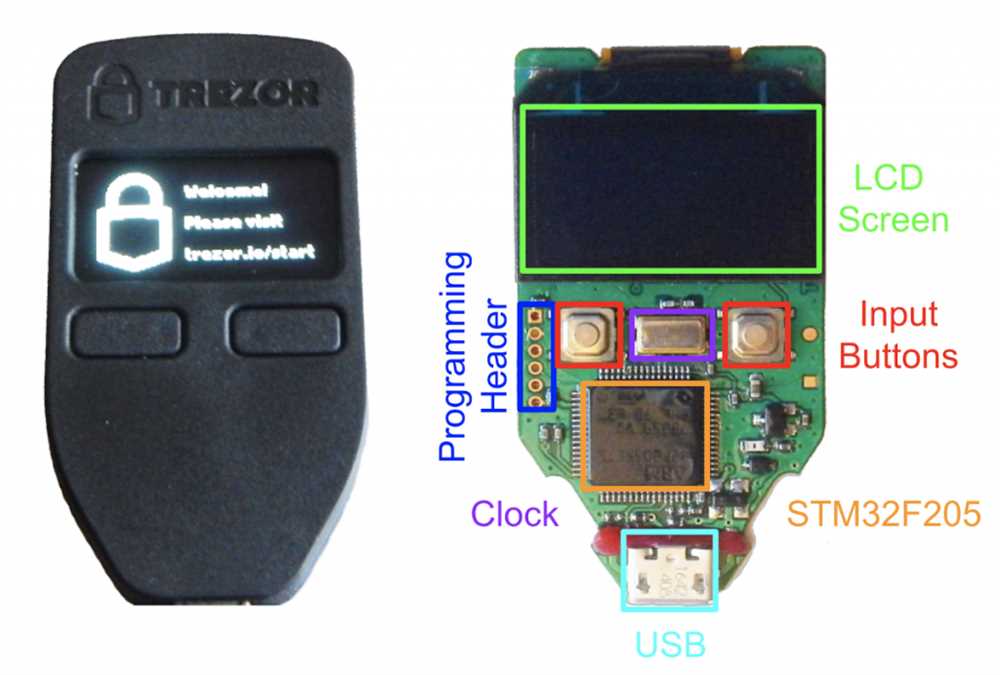
Trezor also utilizes a secure element chip, which is a tamper-resistant hardware component that protects the sensitive information stored on the device. This chip is designed to resist physical attacks, such as tampering or reverse engineering, helping to ensure the integrity of the device and the security of the stored cryptocurrencies.
Furthermore, Trezor regularly releases firmware updates to address any known security vulnerabilities and improve the overall security of the device. Users are encouraged to keep their firmware up to date to benefit from these security enhancements.
The importance of Trezor security cannot be overstated. With the increasing popularity and value of cryptocurrencies, hackers and thieves are constantly looking for ways to exploit vulnerabilities and steal funds. By using a secure hardware wallet like Trezor, users can significantly reduce the risk of their cryptocurrencies being compromised.
| Benefits of Trezor Security |
|---|
| Protection against hacking |
| Secure storage of private keys |
| Multiple layers of security protocols |
| Tamper-resistant hardware component |
| Regular firmware updates |
Common Hacking Techniques Targeting Trezor

When it comes to protecting your funds stored in a Trezor wallet, it’s important to be aware of the common hacking techniques that malicious actors may employ. By understanding these techniques, you can take the necessary precautions to safeguard your cryptocurrency assets.
1. Phishing Attacks: One of the most common hacking techniques targeting Trezor users is phishing. This involves tricking users into providing their confidential information, such as private keys or recovery phrases, through fake websites or emails that mimic the official Trezor interface. It is crucial to always double-check the URL and ensure you are interacting with the legitimate Trezor website.
2. Fake Wallet Apps: Another common hacking technique is the creation of fake wallet apps that mimic the official Trezor app. These apps are often designed to steal users’ private keys or recovery phrases. To avoid falling victim to this type of attack, always download wallet apps from trusted sources, such as official app stores or the Trezor website.
3. Physical Tampering: Malicious individuals may attempt to physically tamper with your Trezor device in order to gain unauthorized access to your funds. This can involve replacing the device with a compromised one or extracting the private keys from the device. It is important to purchase your Trezor device directly from the official website and regularly check for any signs of tampering.
4. Malware and Keyloggers: Hackers may infect your computer or mobile device with malware or keyloggers to steal your cryptocurrency information, including your private keys. It is essential to keep your devices and antivirus software up to date and to exercise caution when downloading files or clicking on suspicious links.
5. Man-in-the-Middle Attacks: In a man-in-the-middle attack, a hacker intercepts communication between you and your Trezor device, allowing them to manipulate transaction data or steal sensitive information. To prevent this type of attack, always ensure you are using secure connections, such as HTTPS, and regularly check for any suspicious activity on your device.
Conclusion: Understanding the common hacking techniques targeting Trezor is essential for safeguarding your cryptocurrency assets. By staying vigilant, double-checking URLs, downloading apps from trusted sources, maintaining the integrity of your Trezor device, keeping your devices secure, and staying mindful of potential man-in-the-middle attacks, you can greatly reduce the risk of falling victim to malicious hackers.
Physical Attacks and the Risk of Heists

Physical attacks on Trezor devices pose a significant risk to the security of stored Bitcoin. These attacks involve accessing the physical hardware or tampering with the device in order to gain unauthorized access to the private keys.
One potential physical attack is the use of brute force to break the device open and access the internal components. This can be done by using tools such as hammers, drills, or other destructive methods. Once the device is open, an attacker can attempt to retrieve the private keys and gain control of the stored Bitcoin.
Another physical attack involves tampering with the device itself. This can include inserting malicious components, such as keyloggers or other hardware designed to intercept the user’s private keys. This type of attack requires physical access to the device and can be difficult to detect.
Physical attacks also include the risk of theft or confiscation of the device. If a Trezor device is stolen, an attacker can attempt to access the private keys and steal the stored Bitcoin. Additionally, if the device is confiscated by authorities, there is a risk that they may attempt to gain access to the private keys for investigative purposes.
To protect against physical attacks and the risk of heists, it is important to keep the Trezor device in a secure location. This can include storing it in a safe or secure lockbox when not in use. It is also important to be cautious of anyone who may have physical access to the device and ensure that it is never left unattended in public places.
| Physical Attacks and the Risk of Heists |
|---|
| 1. Brute force attacks involve breaking the device open and accessing the internal components. |
| 2. Tampering with the device can involve inserting malicious components to intercept private keys. |
| 3. Theft or confiscation of the device can lead to unauthorized access to private keys and stolen Bitcoin. |
Protecting Your Trezor: Best Practices and Security Measures
When it comes to securing your Trezor, the following best practices and security measures are crucial:
1. Firmware Updates: Regularly update your Trezor device with the latest firmware provided by the manufacturer. These updates often include important security patches and bug fixes that enhance the overall security of your device.
2. Strong PIN: Set a strong and unique PIN for your Trezor device. Make sure your PIN is not easily guessable or linked to personal information. Avoid using common patterns or sequences to increase the security of your PIN.
3. Enable Passphrase: Take advantage of the passphrase feature offered by Trezor. This extra layer of security adds an additional, user-defined component to the encryption process. Use a strong passphrase that is unique and not associated with your other passwords.
4. Backup and Recovery: Always create a backup of your Trezor wallet and recovery seed. Store your backup in a secure location, preferably offline. This ensures that you can recover your funds in the event of loss, damage, or theft of your Trezor device.
5. Two-Factor Authentication: Enable two-factor authentication (2FA) whenever possible. This adds an extra layer of security to your account by requiring a secondary verification step, such as a unique code or biometric authentication, in addition to your password.
6. Be Wary of Phishing Attempts: Be vigilant and cautious of emails, websites, or applications that request your Trezor’s sensitive information. Always double-check the authenticity of the source before providing any personal or device-related details.
7. Physical Security: Keep your Trezor device physically secure at all times. Avoid leaving it unattended in public places and consider using a hardware wallet case or safe for added protection.
8. Test Transactions: Before performing any significant transactions, test the process with a small amount first. This allows you to verify the accuracy of the transaction and detect any anomalies before transferring larger sums.
By following these best practices and security measures, you can greatly enhance the safety of your Trezor device and protect your cryptocurrency investments from potential threats.
Q&A:
Is it safe to use a Trezor wallet?
Yes, using a Trezor wallet is generally considered safe. Trezor is a hardware wallet that offers advanced security features to protect your digital assets from hacking attempts and other threats. However, it’s important to always follow best security practices and keep your recovery seed phrase safe to ensure the highest level of security.
What are some potential threats to Trezor wallets?
There are several potential threats to Trezor wallets, including hacking attempts, phishing attacks, physical theft or loss of the device, and vulnerability exploits. Hacking attempts can be mitigated by keeping your firmware up to date and using a strong, unique PIN. Phishing attacks can be avoided by always verifying the authenticity of the Trezor website before entering any sensitive information. Physical theft or loss of the device can be prevented by keeping it in a secure location and creating a backup of your recovery seed. Vulnerability exploits are addressed by regular updates and bug fixes from the Trezor team.


