
Understanding the Challenges of Using Trezor in an Infected Environment

In today’s digital age, the importance of securing our digital assets cannot be overstated. With the rise of cryptocurrencies, keeping our virtual wallets safe from hacking attempts has become a top priority. One popular hardware wallet that provides a secure way to store cryptocurrencies is Trezor.
Trezor is known for its robust security features and offline storage, making it an ideal choice for crypto enthusiasts. However, even with its exceptional security measures, there are challenges that arise when using Trezor in an infected environment.
Operating systems infected with malware or connected to compromised networks pose a significant threat to the security of Trezor. Malware can intercept sensitive information, such as private keys, and compromise the integrity of transactions. This puts the user’s funds at risk and undermines the whole purpose of using Trezor for secure storage.
To mitigate these challenges, it is crucial to understand the potential risks and take appropriate precautions. This article will delve into the specific challenges faced when using Trezor in an infected environment and provide guidance on how to minimize the risks and maximize the security of your digital assets.
Understanding the Importance of Security When Using Trezor
When using a hardware wallet like Trezor, security should always be the top priority. As a device that stores your cryptocurrency private keys, it is crucial to take every precaution to ensure that your funds are safe.
Trezor uses advanced security features to protect your assets. It employs a secure element, which is a tamper-resistant chip that securely stores your private keys. Additionally, it utilizes a secure bootloader, which ensures that the firmware is not compromised during the update process.
However, even with these built-in security measures, it is essential to be vigilant and take additional steps to safeguard your Trezor device. Here are some important security practices to follow:
- Always purchase your Trezor directly from the official website or authorized resellers to avoid counterfeit devices.
- Set up your Trezor in a secure environment, away from prying eyes and potential malware.
- Enable the PIN feature on your Trezor to protect against unauthorized access.
- Regularly update your Trezor firmware to benefit from the latest security enhancements.
- Backup your recovery seed in a secure location and never share it with anyone.
- Use strong and unique passwords for all of your cryptocurrency accounts.
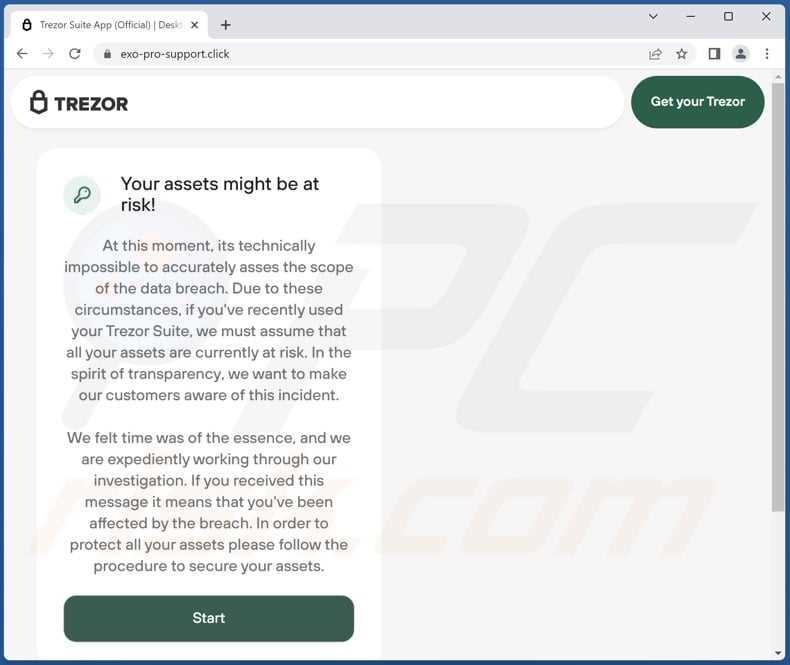
- Be cautious of phishing attempts and always double-check the URL of the websites you visit.
- Consider using a passphrase in addition to your PIN for an extra layer of security.
- Periodically verify the integrity of your Trezor device by performing a self-test.
- Keep your computer and other devices used with Trezor updated with the latest security patches and antivirus software.
By following these security practices, you can greatly minimize the risk of unauthorized access to your Trezor and protect your cryptocurrency investments. Remember, it is your responsibility to prioritize security when dealing with digital assets.
Exploring the Risks of Using Trezor in an Infected Environment

When it comes to storing your cryptocurrency securely, hardware wallets like Trezor are often considered one of the safest options. However, it’s important to understand the risks involved when using Trezor in an infected environment.
An infected environment refers to a computer or device that has been compromised by malware or other malicious software. This can include keyloggers, remote access trojans, or other types of malware that are designed to steal sensitive information.
Using Trezor in an infected environment can expose your private keys and seed phrases to potential theft. Since hardware wallets are used to sign transactions and provide an extra layer of security, they are also a prime target for attackers. If the device you’re using to access your Trezor wallet is infected, it’s possible for an attacker to intercept your private keys and gain access to your funds.
One of the main risks of using Trezor in an infected environment is the potential for a “man-in-the-middle” attack. In this type of attack, the malware on your device can intercept and modify the communication between your Trezor device and your computer. This can allow the attacker to manipulate the transaction details and redirect funds to their own wallet.
Another risk is the possibility of the malware capturing your seed phrase or recovery words. This information is used to restore access to your wallet in case your Trezor device is lost or damaged. If an attacker gains access to your seed phrase, they can easily restore your wallet on their own Trezor device and gain full control over your funds.
To mitigate these risks, it’s important to ensure that the device you’re using to access your Trezor wallet is free from malware. Regularly scan your computer or device for viruses and malware, and only use it for cryptocurrency-related activities. Avoid downloading software or visiting suspicious websites that may contain malware.
Additionally, consider using a dedicated computer or device solely for accessing your Trezor wallet. This can decrease the chances of your device being infected with malware that could compromise your funds.
Overall, while Trezor offers strong security measures for storing your cryptocurrency, using it in an infected environment can expose you to significant risks. It’s crucial to stay vigilant and take necessary precautions to protect your private keys and seed phrase from potential theft.
Protecting Your Trezor Wallet from Malware and Phishing Attacks

When using your Trezor wallet, it is important to take precautions to protect it from malware and phishing attacks. These attacks can compromise the security of your wallet and result in the loss of your cryptocurrency.
Here are some steps you can take to protect your Trezor wallet:
- Keep your computer and software up to date: Keeping your operating system, antivirus software, and web browsers up to date is essential in protecting your Trezor wallet. Updates often include security patches that can prevent malware and phishing attacks.
- Only download software from trusted sources: To avoid malware, only download software, including wallets or any supporting applications, from the official Trezor website or other trusted sources. Be cautious of downloading software from unknown or unverified sources.
- Double-check URLs: When accessing your Trezor wallet online, always double-check the URL to ensure you are visiting the official website. Be cautious of phishing attempts that mimic legitimate websites to trick you into entering your wallet details.
- Enable two-factor authentication: Two-factor authentication adds an extra layer of security to your Trezor wallet. Enable this feature to require an additional verification step, such as a one-time password sent to your mobile device, when logging in or performing transactions.
- Be cautious of email and social media scams: Phishing attacks often occur through email or social media platforms. Be wary of unsolicited emails or messages asking for your wallet details or providing links to suspicious websites. Never click on suspicious links or provide personal information.
- Use hardware wallets: Hardware wallets like Trezor provide an added layer of security by keeping your private keys offline. This reduces the risk of your wallet being compromised by malware or phishing attacks.
- Regularly back up your wallet: Regularly backing up your wallet ensures that even if your device is compromised, you can still restore your funds. Follow the backup instructions provided by Trezor and securely store your backup in a separate location.
- Be cautious of public Wi-Fi: Avoid accessing your Trezor wallet on public Wi-Fi networks, as they can be insecure. If you must use public Wi-Fi, consider using a virtual private network (VPN) to encrypt your connection and protect your data.
- Educate yourself: Stay informed about the latest threats and security best practices. By educating yourself on common attack methods and being aware of potential risks, you can better protect your Trezor wallet.
By following these steps, you can significantly reduce the risk of malware and phishing attacks on your Trezor wallet. Remember to always prioritize the security of your wallet and funds, and remain vigilant when using your wallet in any environment.
Best Practices for Safely Using Trezor in a Potentially Unsafe Environment
When using Trezor in a potentially unsafe environment, such as a public Wi-Fi network or a computer that may be infected with malware, it is important to follow best practices to ensure the security of your cryptocurrency holdings. Below are some recommended steps to take:
1. Use a Secure Internet Connection

Whenever possible, use a known and trusted internet network to connect your Trezor device. Avoid using public Wi-Fi networks, as they may be vulnerable to hacking attempts or malicious activities.
2. Keep Your Device’s Firmware Up to Date
Regularly check for firmware updates on the official Trezor website and install them promptly. Firmware updates often include important security patches that can help protect against new threats and vulnerabilities.
3. Verify Address on Device
When initiating a transaction, always verify the receiving address on your Trezor device’s screen. This ensures that you are sending funds to the intended recipient and not to a malicious address that could be displayed on an infected computer or website.
4. Enable Passphrase Protection

Consider enabling the passphrase feature on your Trezor device. This provides an additional layer of security by requiring a passphrase to access your accounts. Make sure to choose a strong and unique passphrase that is not easily guessable.
5. Run Antivirus and Malware Scans

Regularly scan your computer for any viruses, malware, or other malicious software. Use reputable antivirus software and keep it up to date. This can help detect and remove any potential threats that may compromise the security of your Trezor device.
By following these best practices, you can enhance the security of your Trezor device and minimize the risks associated with using it in a potentially unsafe environment.
Q&A:
What are the challenges of using Trezor in an infected environment?
The main challenge of using Trezor in an infected environment is the risk of exposing your private keys and sensitive information to malware or hackers. Malicious software can potentially intercept the communication between your computer and Trezor device, compromising the security of your funds.
How can my Trezor be compromised in an infected environment?
Your Trezor device can be compromised in an infected environment if you connect it to a compromised or infected computer. Malware or keyloggers on your computer can potentially capture your passphrase or PIN when you enter it on a compromised system. This information can then be used by attackers to gain access to your funds.
What precautions should I take when using Trezor in an infected environment?
When using Trezor in an infected environment, it is important to ensure that you have a clean and secure computer. This may involve using a separate computer or dedicated hardware wallet device, such as Trezor Model T, that has additional security features. Additionally, always double-check the authenticity of the Trezor firmware and software updates to avoid installing any malicious versions.


