
Trezor’s Security Breach: Future of Hardware Wallets

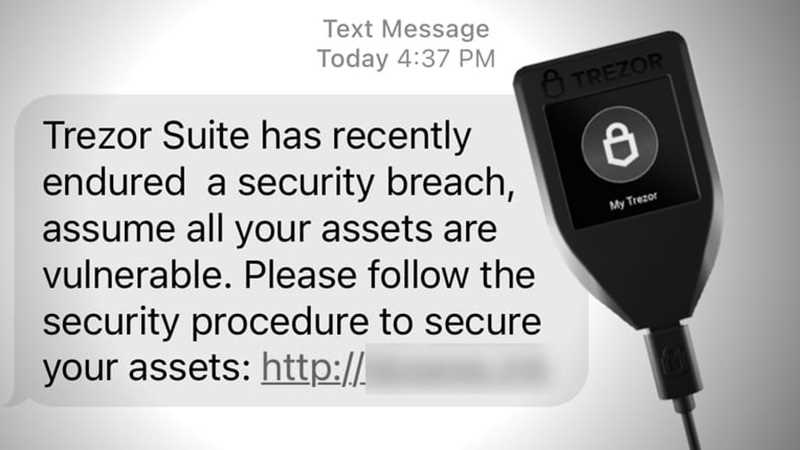
In the fast-evolving world of cryptocurrency, security has always been a concern. The recent security breach of Trezor, one of the leading hardware wallet providers, has sent shockwaves throughout the industry. This breach has exposed the vulnerabilities of hardware wallets and has raised questions about their effectiveness in safeguarding digital assets. As more and more people turn to hardware wallets to secure their cryptocurrencies, this breach is a wake-up call for both users and manufacturers.
Trezor’s security breach was not just a minor incident. It revealed a flaw in the design of their hardware wallets that allowed hackers to retrieve sensitive information and gain access to users’ funds. This breach has shattered the trust of many cryptocurrency enthusiasts who believed that using a hardware wallet would provide an impenetrable fortress for their investments.
While Trezor has taken immediate action to address the issue and provide necessary updates to their products, the impact of this breach is irreversible. It has forced the industry as a whole to reevaluate the security measures implemented in hardware wallets and find better solutions to protect users from such attacks. The traditional notion of hardware wallets being the most secure option is now being challenged, and users are left wondering if there is a truly foolproof solution to safeguard their digital assets.
As hardware wallet manufacturers scramble to improve their products’ security, cryptocurrency enthusiasts must also take a proactive approach in protecting their investments. It is crucial for users to employ additional security measures, such as multi-factor authentication and regular firmware updates, to minimize the risk of such breaches. Furthermore, users should stay informed about the latest security developments and choose hardware wallets from reputable manufacturers that prioritize security and actively address vulnerabilities.
Trezor’s security breach serves as a game changer for the hardware wallet industry. It has highlighted the need for constant innovation and improvement in security measures to preserve users’ trust and protect their valuable digital assets. As the industry moves forward, it is critical for manufacturers and users to collaborate and work towards developing advanced security solutions that leave no room for compromises.
The Impact of Trezor’s Security Breach
The security breach at Trezor, a popular hardware wallet for storing cryptocurrencies, has had a significant impact on the cryptocurrency community and the perception of hardware wallets as a secure means of storing digital assets.
User Confidence Shaken

The security breach has shaken the confidence of users who rely on hardware wallets to keep their cryptocurrencies safe. Many users regarded hardware wallets as the most secure option for storing their digital assets, but this incident has raised doubts about their reliability and effectiveness.
This breach has highlighted the fact that no system is entirely immune to attacks, and even hardware wallets can be compromised. Users are now questioning the security measures implemented by hardware wallet manufacturers and are looking for alternative solutions to safeguard their investments.
Increased Demand for Additional Security Measures
The Trezor security breach has also led to an increased demand for additional security measures to be implemented by hardware wallet manufacturers. Users are now looking for features such as multi-factor authentication, biometric verification, and enhanced encryption methods to ensure the safety of their digital assets.
Hardware wallet manufacturers will need to respond to this demand by incorporating these advanced security measures into their products or risk losing customers to competitors who can provide more robust security features.
Implications for the Cryptocurrency Industry

The security breach at Trezor has broader implications for the cryptocurrency industry as a whole. It highlights the need for stronger security measures across all aspects of the industry, including wallet providers, exchanges, and other service providers.
Investors and users are now more aware of the risks associated with storing and trading cryptocurrencies, which could lead to increased regulatory scrutiny and the implementation of stricter security guidelines. It may also drive the development of new security technologies and protocols to better protect digital assets.
- The breach serves as a wake-up call for individuals and companies involved in the cryptocurrency space, emphasizing the importance of constant vigilance and proactive security measures.
- It also serves as a reminder that security is a shared responsibility, and users must take steps to protect their own digital assets by adopting best practices such as using strong passwords, enabling two-factor authentication, and regularly updating software and firmware.
- Ultimately, the impact of Trezor’s security breach will lead to a more secure cryptocurrency ecosystem, with increased awareness, improved security measures, and a greater emphasis on user education and protection.
Evaluating the Vulnerabilities in Trezor’s Hardware Wallet
With the recent security breach at Trezor, it is important to closely examine the vulnerabilities in their hardware wallet. By understanding these weaknesses, users can make informed decisions about their cryptocurrency storage options.
1. Physical Attack Vulnerabilities

Trezor’s hardware wallet is designed to be secure against physical attacks, but no device is completely impervious to tampering. It is important to consider the various physical attack vectors that could compromise the device’s security:
- Malicious tampering with the device’s hardware components
- Physical extraction of data from the device
- Secret keys potentially being exposed during transportation or storage
2. Firmware Vulnerabilities
Trezor’s firmware is regularly updated to address security vulnerabilities, but new vulnerabilities can always emerge. It is crucial to analyze potential firmware vulnerabilities to assess the overall security of the hardware wallet:
- Unpatched vulnerabilities that could be exploited by attackers
- Malicious firmware updates that could compromise the device
- Insufficient verification processes for firmware updates
Overall, the vulnerabilities in Trezor’s hardware wallet should be thoroughly evaluated before making a decision about its usage. It is recommended to stay informed about any security updates from the manufacturer and to follow best practices for securing cryptocurrency assets.
The Need for Enhanced Security Measures in Hardware Wallets

With the recent security breach at Trezor, the need for enhanced security measures in hardware wallets has become a pressing concern. As hardware wallets are designed to securely store private keys and facilitate transactions, any vulnerabilities can result in the loss or theft of valuable cryptocurrency assets.
The breach at Trezor, a popular hardware wallet manufacturer, revealed the risks associated with relying solely on hardware security. It highlighted the fact that even the most reputable companies can suffer from security flaws that can compromise the safety of users’ funds.
Physical Security
One area where hardware wallets need enhanced security is in physical protection. While hardware wallets are generally more secure than software wallets, they are still vulnerable to physical tampering. The recent breach at Trezor involved exploiting a vulnerability in the chip used in the wallet, demonstrating the importance of strengthening physical security measures.
Hardware wallets could benefit from increased tamper-proofing techniques, such as stronger casings, tamper-evident seals, and enhanced methods of detecting physical tampering. Implementing measures to detect and mitigate physical attacks can significantly reduce the risk of unauthorized access to private keys.
Firmware Security

Another area that requires enhanced security is firmware. Firmware is responsible for managing the operations and security of the hardware wallet. However, vulnerabilities in firmware can expose users to various attacks, such as keyloggers or malware injection.
Hardware wallet manufacturers need to invest more resources in comprehensive firmware security testing and regular updates. This includes conducting thorough code audits, implementing secure coding practices, and promptly addressing any identified vulnerabilities.
Additionally, hardware wallets could benefit from mechanisms that allow users to verify the authenticity and integrity of firmware updates. This would help prevent users from unknowingly installing compromised firmware that could compromise the security of their funds.
In conclusion, the recent security breach at Trezor has emphasized the need for enhanced security measures in hardware wallets. Strengthening physical security and ensuring robust firmware security are crucial steps towards providing users with a secure storage solution for their cryptocurrency assets. Hardware wallet manufacturers must prioritize these security measures to maintain the trust of their users and protect their valuable funds.
The Future of Hardware Wallets: Ensuring User Confidence and Trust

Hardware wallets have long been considered one of the most secure ways to store cryptocurrencies. However, the recent security breach of Trezor’s hardware wallet has raised concerns about the safety of these devices.
In light of this incident, it is crucial for the industry to address the vulnerabilities of hardware wallets and take steps to ensure user confidence and trust. Here are some key considerations for the future of hardware wallets:
Enhanced Security Measures

Hardware wallet manufacturers need to prioritize enhanced security measures to prevent similar breaches in the future. This includes implementing robust encryption algorithms, conducting regular security audits, and actively addressing any identified vulnerabilities.
Furthermore, two-factor authentication should become a standard feature of hardware wallets. This multi-layered approach to security adds an extra level of protection, making it significantly more difficult for attackers to gain unauthorized access to users’ funds.
Improved User-Friendly Interfaces
While security is of utmost importance, it’s equally crucial for hardware wallets to have user-friendly interfaces. Complex setups and confusing processes can discourage new users from adopting these devices.
Manufacturers should focus on streamlining the setup and recovery processes, providing clear instructions, and designing intuitive interfaces. This will make hardware wallets more accessible to a wider range of users, ultimately increasing adoption rates and further securing the cryptocurrency ecosystem.
Transparency and Open Source Development
Another key factor in ensuring user confidence and trust is transparency. Hardware wallet manufacturers should prioritize open-source development, allowing independent audits of their code and firmware. This will help detect any potential vulnerabilities and strengthen the overall security of the devices.
By openly sharing their development processes and engaging with the community, hardware wallet manufacturers can foster trust among users and demonstrate their commitment to security.
In conclusion, the recent security breach of Trezor’s hardware wallet has highlighted the need for ongoing improvements in the industry. Enhanced security measures, improved user-friendly interfaces, and a commitment to transparency are key factors that will shape the future of hardware wallets. By addressing these concerns, the industry can rebuild user confidence and ensure that hardware wallets remain a trusted and secure solution for storing cryptocurrencies.
Q&A:
What is Trezor?
Trezor is a hardware wallet that allows users to securely store their cryptocurrency offline.
What happened in Trezor’s security breach?
Trezor experienced a security breach where an attacker gained physical access to the device and was able to extract sensitive information from it.
How does this security breach affect the security of hardware wallets?
This security breach is a game changer for hardware wallets as it raises concerns about the overall security of such devices. Users are now questioning whether hardware wallets are truly secure and if they can trust them to protect their cryptocurrency.
What steps is Trezor taking to prevent future security breaches?
Trezor has stated that they are taking steps to prevent future security breaches, such as implementing additional security measures and improving the physical security of their devices. They are also working on enhancing the firmware of their devices to make them more resilient to attacks.


