
The Dark Web Connection: Uncovering the Fate of the Stolen Trezor Wallet Data

When it comes to keeping our digital assets safe, securing our cryptocurrencies is of utmost importance. Trezor, the popular hardware wallet, has long been regarded as one of the most secure options out there. However, recent events have raised concerns about the safety of Trezor wallet data and its possible connection to the dark web.
In a shocking revelation, it has been discovered that a significant amount of Trezor wallet data has been stolen and is now being traded on the dark web. This stolen data includes private keys, mnemonic phrases, and other sensitive information that could grant unauthorized access to users’ cryptocurrency holdings.
The dark web, a hidden part of the internet that is not accessible through traditional search engines, is notorious for its involvement in illegal activities. It is a hub for criminal activities, including the buying and selling of stolen data. The stolen Trezor wallet data has found its way onto these underground marketplaces, where criminals are attempting to profit from it.
The implications of this breach are profound. If the stolen Trezor wallet data falls into the wrong hands, it could result in substantial financial loss for affected individuals. Cryptocurrency theft has become a widespread issue, and with the involvement of the dark web, the risks are even higher.
Efforts are being made to track down the criminals responsible for the theft and put an end to this illegal trade. Security experts are working tirelessly to uncover the dark web connections and shut down the marketplaces where the stolen Trezor wallet data is being traded. Additionally, users are urged to take precautionary measures, such as changing their passwords and enabling two-factor authentication, to protect their digital assets from falling into the wrong hands.
Understanding the Stolen Trezor Wallet Data
The theft of the Trezor wallet data has raised concerns in the cryptocurrency community. To fully grasp the implications of this incident, it is essential to understand the stolen Trezor wallet data and its potential impact.
What is Trezor Wallet Data?

Trezor is a popular hardware wallet that allows users to securely store their cryptocurrencies offline. The wallet data refers to the information stored on these devices, including private keys, addresses, and transaction history.
Implications of the Stolen Trezor Wallet Data
The theft of the Trezor wallet data can have serious consequences for the affected individuals. Here are some potential implications:
| 1. Theft of Funds | The stolen wallet data can be used to access and transfer funds from the compromised wallets. This puts the owners’ cryptocurrency holdings at risk. |
|---|---|
| 2. Identity Theft | With access to the stolen wallet data, malicious actors can potentially steal the owners’ identities, leading to other types of financial fraud. |
| 3. Privacy Breach | The compromised wallet data may contain sensitive information about the owners’ transactions and holdings, compromising their privacy. |
| 4. Trust Issues | The incident may erode trust in hardware wallets like Trezor, causing users to question the security of their cryptocurrency storage solutions. |
It is crucial for Trezor users to take appropriate actions, such as changing their passwords, enabling two-factor authentication, and monitoring their accounts for any suspicious activity.
In conclusion, the stolen Trezor wallet data poses significant risks to the affected individuals, including theft of funds, identity theft, privacy breach, and trust issues. It is essential for users to stay vigilant and take necessary precautions to protect their cryptocurrency holdings.
The Extent of the Theft and Its Implications
The theft of the Trezor wallet data was a significant event with far-reaching implications for both the affected users and the broader cryptocurrency community. This act of cybercrime highlighted the vulnerabilities of the digital wallet ecosystem and raised questions about the security measures implemented by various wallet providers.
According to reports, the stolen data included sensitive information such as private keys, transaction history, and wallet addresses. This type of data can empower hackers with the ability to access and transfer the funds stored in these wallets, potentially resulting in substantial financial losses for the affected individuals.
Furthermore, the stolen data presents a significant risk to the overall security of the affected users. With access to private keys, hackers can impersonate the owners of the wallets and engage in fraudulent activities. This poses a threat not only to the affected individuals but also to the reputation and trustworthiness of the blockchain technology.
It is essential to note that the implications of this theft extend beyond the immediate financial losses. The stolen data is likely to appear on the dark web, where it can be bought and sold by cybercriminals. This not only reinforces the existence of a thriving black market for stolen cryptocurrency assets but also raises concerns about the potential misuse of the stolen data in other criminal activities.
To assess the full extent of the theft, it is crucial to understand the scale of the data breach. Reports indicate that thousands of Trezor wallet holders may have been affected. This number signifies a significant breach of personal data, prompting users to reevaluate their security practices and consider additional measures to safeguard their assets.
As a result of this incident, wallet providers and cryptocurrency exchanges are expected to review and enhance their security protocols. This theft serves as a wake-up call for the industry, highlighting the need for robust security measures to protect the funds and data of their users.
| Key Takeaways |
|---|
| The theft of Trezor wallet data has wide-ranging implications for affected users and the cryptocurrency community. |
| The stolen data includes private keys, transaction history, and wallet addresses, leaving affected individuals vulnerable to financial losses and identity theft. |
| The stolen data may appear on the dark web, potentially fueling further criminal activities. |
| Thousands of Trezor wallet holders may have been affected, highlighting the urgent need for enhanced security measures. |
| This incident serves as a wake-up call for the industry, prompting wallet providers to review and strengthen their security protocols. |
The Dark Web’s Involvement in Stolen Trezor Wallet Data
As the popularity of cryptocurrencies continues to rise, so does the interest among cybercriminals. Trezor, one of the leading hardware wallet providers, has become a target for these criminals due to its high-security reputation. Recently, there have been reports of stolen Trezor wallet data circulating on the dark web.
The dark web, a hidden part of the internet, is notorious for facilitating various illegal activities, including the sale and trade of stolen data. It provides a platform for cybercriminals to operate under a veil of anonymity, making it difficult for law enforcement agencies to track them down.
The Stolen Trezor Wallet Data
It appears that the stolen Trezor wallet data primarily consists of wallet addresses and associated passwords. These details can be used by cybercriminals to gain unauthorized access to a user’s cryptocurrency assets. With the rising value of cryptocurrencies, the stakes are high, making this stolen data extremely valuable on the black market.
It’s important to note that the stolen data does not include the private keys or recovery seeds, which are crucial for accessing and recovering the funds stored in a Trezor wallet. However, even without these vital pieces of information, cybercriminals can still cause significant harm by attempting to crack the passwords or by using social engineering techniques to trick users into revealing their private keys.
The Role of the Dark Web
The dark web acts as a marketplace where stolen Trezor wallet data is bought and sold. Cybercriminals looking to profit from the stolen information can find potential buyers and negotiate transactions anonymously. This underground economy thrives on the trust established within its illicit community, allowing criminals to trade data without fear of being caught.
Law enforcement agencies around the world are aware of the dark web’s involvement in the sale of stolen data and have been working tirelessly to infiltrate these criminal networks. However, due to the anonymous nature of the dark web, investigations are often complex and time-consuming.
The dark web’s involvement in the stolen Trezor wallet data highlights the need for enhanced cybersecurity measures and user awareness. Users should prioritize strong passwords, avoid sharing sensitive information online, and stay updated on the latest security practices.
To safeguard against stolen wallet data, users are also encouraged to regularly update their wallet’s firmware and ensure they are using the latest security features offered by Trezor.
By understanding the dark web’s involvement in the stolen Trezor wallet data, users can better protect their assets and contribute to the ongoing efforts against cybercrime.
An Inside Look at the Investigation into the Stolen Trezor Wallet Data
The theft of the Trezor wallet data sent shockwaves through the cryptocurrency community. As soon as the news broke, investigators went into action to uncover the truth behind this heinous crime. This article provides an inside look into the investigation and the steps taken to trace the stolen Trezor wallet data.
Securing the Crime Scene
The first step in any investigation is to secure the crime scene. In the case of the stolen Trezor wallet data, this meant isolating and preserving any devices or systems that could potentially contain evidence. Investigators carefully examined the affected systems and collected any available data, ensuring the preservation of chain of custody.
Tracing the Dark Web Connection
It soon became clear that the stolen Trezor wallet data was being sold on the dark web. Investigators began their search in various underground forums and marketplaces, utilizing both human intelligence and advanced technological tools. This involved monitoring websites, infiltrating chat rooms, and even conducting undercover transactions to gather evidence.
Through their tireless efforts, investigators were able to trace the dark web connection to a sophisticated cybercriminal operation. The stolen wallet data was being bought and sold by a network of hackers who had gained unauthorized access to several high-profile cryptocurrency exchanges.
Collaboration with Law Enforcement Agencies

As the investigation progressed, law enforcement agencies from different countries joined forces to bring down the cybercriminal operation responsible for the theft. International cooperation was crucial in sharing information, coordinating arrests, and conducting raids on the criminal network’s hideouts.
Thanks to this collaboration, several key members of the cybercriminal network were apprehended, and a significant amount of the stolen Trezor wallet data was recovered. The joint efforts of investigators and law enforcement agencies dealt a severe blow to the dark web marketplace for stolen cryptocurrency information.
Conclusion
The investigation into the stolen Trezor wallet data was a complex and challenging undertaking. Through meticulous analysis, relentless pursuit of evidence, and international collaboration, law enforcement agencies were able to disrupt the dark web market for stolen cryptocurrency information. This case serves as a reminder of the importance of cybersecurity and the constant need to stay one step ahead of cybercriminals.
Protecting Your Trezor Wallet and Preventing Data Theft
To ensure the safety of your Trezor wallet and prevent any potential data theft, it is crucial to follow best practices and implement strong security measures. Here are some steps you can take to protect your Trezor wallet:
1. Keep your recovery seed secure: The recovery seed is an essential component of your Trezor wallet, as it allows you to recover your funds in case of loss or theft. Make sure to store it safely in a secure location, preferably offline and away from prying eyes.
2. Enable PIN protection: Set a PIN code for your Trezor wallet to add an extra layer of security. Make sure to choose a PIN that is not easily guessable and avoid using common combinations such as birthdays or sequential numbers.
3. Create a strong password: When setting up your Trezor wallet, use a strong and unique password to protect your device and the associated software. Avoid reusing passwords from other accounts and consider using a password manager to securely store your passwords.
4. Keep your firmware up to date: Regularly check for firmware updates and install them as soon as they become available. These updates often include security patches and bug fixes that help protect your Trezor wallet against potential vulnerabilities.
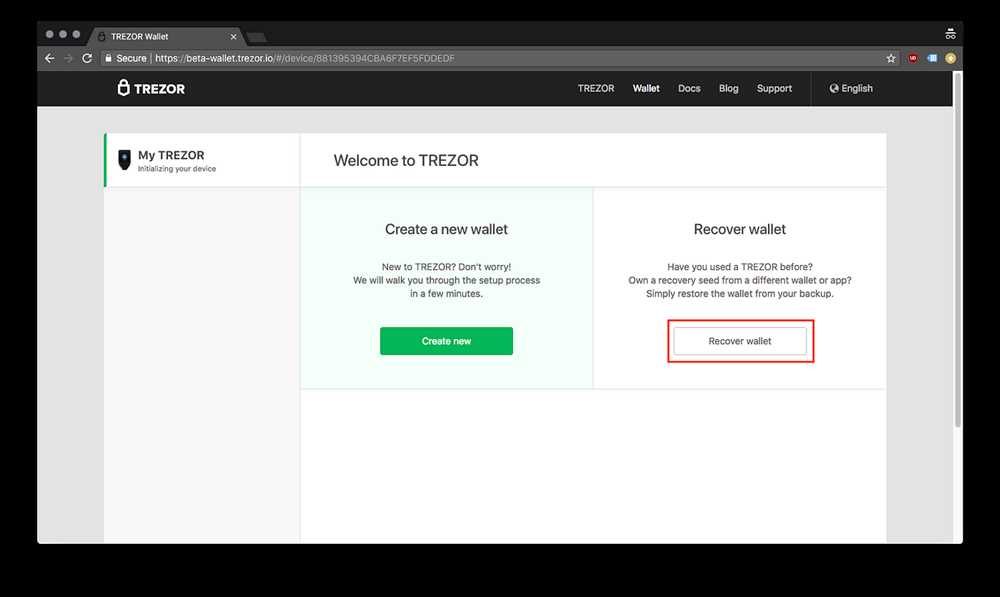
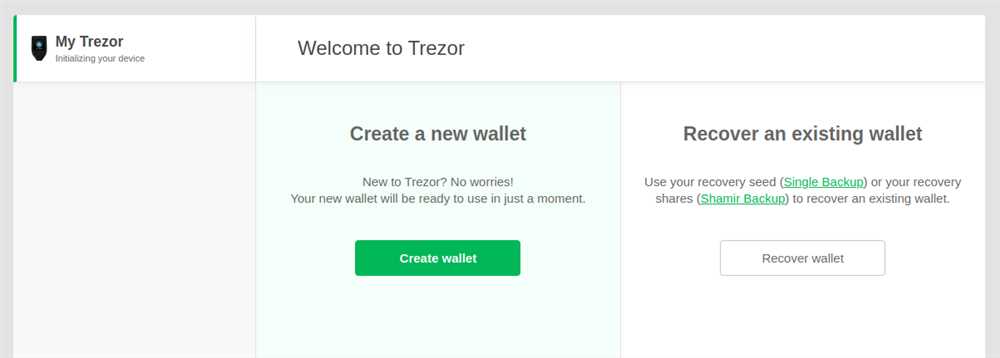
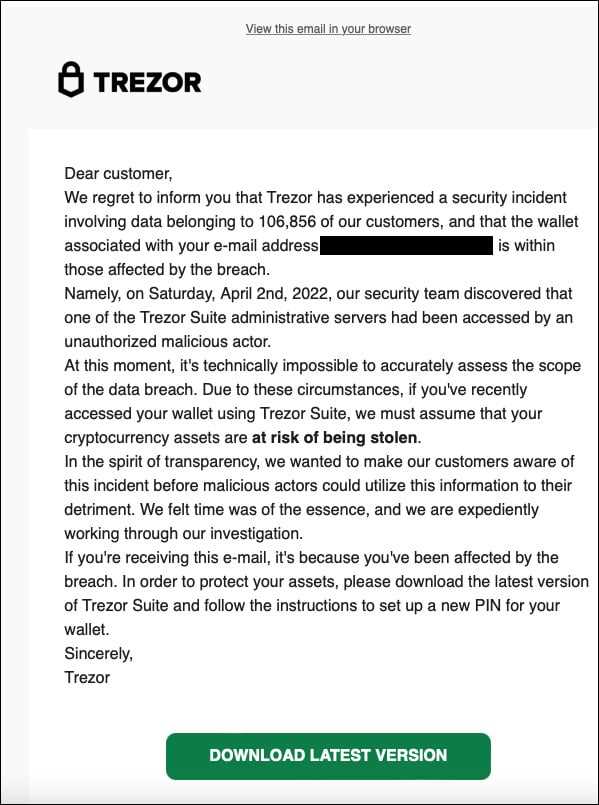
5. Be cautious of phishing attempts: Beware of phishing emails, websites, or apps that mimic the official Trezor wallet interface. Always double-check the URL and ensure that you are accessing the genuine Trezor website or software before entering any sensitive information.
6. Use a secure connection: When accessing your Trezor wallet or conducting any transactions, make sure to use a secure and trusted internet connection. Avoid using public or unsecured networks, as they can potentially expose your data to hackers.
By following these security measures, you can significantly reduce the risk of data theft and ensure the safety of your Trezor wallet. Remember to stay vigilant and regularly update yourself with the latest security practices to stay one step ahead of potential threats.
Q&A:
What is the Trezor wallet data breach that this article talks about?
The Trezor wallet data breach refers to the incident where an attacker gained unauthorized access to Trezor’s customer database and stole sensitive information, including user email addresses and encrypted passwords.
How did the attacker gain access to the Trezor customer database?
The exact details of how the attacker gained access to the Trezor customer database are not mentioned in the article. However, it is speculated that the attacker may have exploited a vulnerability in the system or used a phishing attack to trick users into revealing their login credentials.
What is the dark web connection mentioned in the article?
The dark web connection mentioned in the article refers to the fact that the stolen Trezor wallet data was found being sold on the dark web. This means that the attacker who stole the data has likely sold it to other individuals or hackers on the dark web, making it even more difficult to trace and recover the stolen information.


