How to Safeguard Your Cryptocurrency with the Trezor Wallet: A Step-by-Step Guide
With the increasing popularity of cryptocurrencies, it is essential to secure your digital assets from potential threats. One of the most effective ways to protect your cryptocurrency is by using a hardware wallet. Trezor, a trusted name in the crypto community, offers a secure and user-friendly solution that allows you to store and manage your digital currencies.
Trezor is a hardware wallet that provides an extra layer of security by keeping your private keys offline. This means that your sensitive information is never exposed to the internet, making it virtually impossible for hackers to access your funds. With Trezor, you can have peace of mind knowing that your cryptocurrency is safe from online attacks.
Setting up your Trezor wallet is straightforward and does not require any technical expertise. Simply connect the device to your computer or mobile phone, follow the on-screen instructions, and create a unique PIN. Once your wallet is set up, you can start sending, receiving, and storing your cryptocurrencies with ease.
Trezor supports a wide range of cryptocurrencies, including Bitcoin, Ethereum, Litecoin, and many more. It also integrates with popular cryptocurrency management platforms, allowing you to keep track of your portfolio and make transactions directly from your wallet. With its intuitive interface and robust security features, Trezor is an excellent choice for both beginner and experienced cryptocurrency users.
In conclusion, securing your cryptocurrency is of utmost importance in today’s digital world. By using the Trezor wallet, you can protect your digital assets from potential threats and have full control over your funds. Its easy setup process and extensive support for various cryptocurrencies make it a top choice among crypto enthusiasts. Don’t take any chances with your valuable digital assets – invest in a Trezor wallet today!
What is a Trezor Wallet?
A Trezor Wallet is a hardware wallet designed to securely store your cryptocurrency. It is a small device that looks like a USB stick and connects to your computer via a USB cable. This wallet is known for its high level of security and is recommended for anyone who wants to keep their digital assets safe and protected.
Unlike software wallets that are vulnerable to hacking and malware attacks, a Trezor Wallet operates offline, meaning it is not connected to the internet when you use it. This greatly reduces the risk of your private keys being exposed to potential hackers or malware.
Key Features of Trezor Wallet

1. Secure Storage: The Trezor Wallet stores your private keys and keeps them safe from online threats. It uses advanced security measures such as encryption and PIN protection to ensure that your funds cannot be accessed by anyone else.
2. Compatibility: The Trezor Wallet is compatible with a wide range of cryptocurrencies, including Bitcoin, Ethereum, Litecoin, and many others. This makes it a versatile option for users who hold multiple types of digital assets.
3. Easy to Use: Despite its advanced security features, the Trezor Wallet is designed to be user-friendly. It has a simple and intuitive interface that allows even beginners to easily navigate and manage their cryptocurrencies.
4. Backup and Recovery: In case your Trezor Wallet gets lost or damaged, you can easily recover your funds using the recovery seed provided during the setup process. This ensures that your assets are never permanently lost, even if the device itself is compromised.
5. Open Source: The Trezor Wallet is an open-source project, which means that its software code can be reviewed and audited by anyone. This transparency adds an extra layer of trust, as it allows the community to verify the security of the wallet and identify any potential vulnerabilities.
In summary, a Trezor Wallet is a secure and easy-to-use hardware wallet that provides a high level of protection for your cryptocurrency. Whether you are a beginner or an experienced user, using a Trezor Wallet ensures that your digital assets remain safe and under your control.
Why Use a Trezor Wallet?
When it comes to storing and securing your cryptocurrency, it is of utmost importance to choose a trusted and reliable wallet. One such wallet that has gained a reputation as one of the best options for storing cryptocurrencies is the Trezor Wallet.
Here are some reasons why you should consider using a Trezor Wallet:
1. Security:
Trezor Wallet provides a high level of security for your cryptocurrencies. It uses advanced security measures, such as multi-signature authentication, to ensure that only you have access to your funds. Additionally, the wallet generates a unique private key for each transaction, making it virtually impossible for hackers to steal your coins.
2. User-Friendly Interface:
The Trezor Wallet has a user-friendly interface that makes it easy to navigate and use. Whether you are a beginner or an experienced cryptocurrency user, you will find the wallet intuitive and straightforward.
3. Support for Multiple Cryptocurrencies:
Trezor Wallet supports a wide range of cryptocurrencies, including Bitcoin, Ethereum, Litecoin, and more. This means that you can use the wallet to store all your favorite cryptocurrencies in one place, without the need for multiple wallets.
4. Offline Storage:
One of the biggest advantages of using a Trezor Wallet is that it stores your cryptocurrencies offline. This offline storage, also known as “cold storage,” ensures that your funds are safe from online threats, such as hacking and phishing attacks.
In conclusion, using a Trezor Wallet is a wise choice if you want to secure your cryptocurrency holdings. Its advanced security features, user-friendly interface, and support for multiple cryptocurrencies make it an ideal choice for both beginners and experienced users. So, why take chances with the security of your digital assets when you can use the trusted and reliable Trezor Wallet?
How to Set Up a Trezor Wallet

Setting up a Trezor wallet is a straightforward process that requires a few simple steps. Follow the instructions below to get started:
Step 1: Prepare the Trezor Device
- Connect your Trezor device to your computer or mobile device using the provided USB cable.
- Make sure your device is fully charged or connected to a power source.
Step 2: Access the Trezor Wallet

- Visit the official Trezor website (https://trezor.io/) and click on the “Get started” button.
- Follow the on-screen instructions to install the Trezor Bridge software, which allows your device to communicate with the Trezor wallet interface.
- Once the installation is complete, launch the Trezor Wallet by clicking on the “Connect Trezor” button.
Step 3: Set Up Your Trezor Wallet

- Choose a pin for your Trezor device and enter it when prompted. Make sure to choose a strong pin and remember it, as it will be required every time you access your wallet.
- Generate a recovery seed by following the instructions provided on the screen. This seed is essential for recovering your wallet in case your Trezor device is lost or damaged.
- Verify the recovery seed by entering the words in the correct order when prompted. This step ensures that you’ve correctly noted down the recovery seed.
That’s it! You’ve successfully set up your Trezor wallet. Now you can start using it to securely store and manage your cryptocurrencies. Make sure to keep your pin and recovery seed in a safe place and never share them with anyone.
Best Practices for Using a Trezor Wallet

Using a Trezor wallet is one of the safest ways to store and manage your cryptocurrency. However, to ensure maximum security and protect your funds, it is important to follow best practices when using a Trezor wallet.
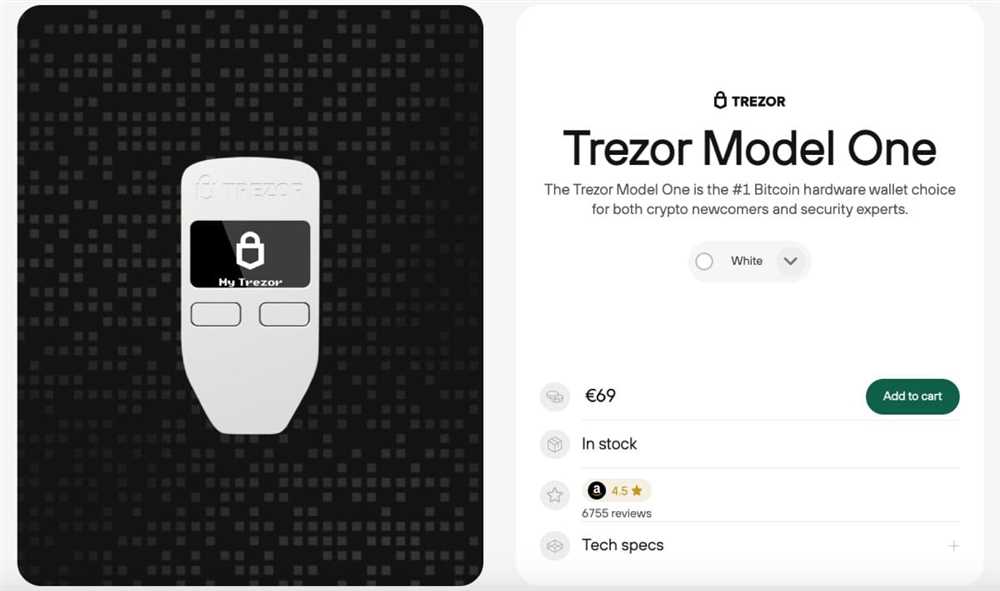
1. Purchase from the Official Website
When buying a Trezor wallet, always make sure to purchase it directly from the official website. This will ensure that you receive an authentic device and not a counterfeit one. Additionally, it is important to verify the authenticity of the device upon receipt.
2. Set Up the Wallet Securely
During the initial setup of your Trezor wallet, it is crucial to follow all the recommended security measures. This includes using a strong and unique PIN, enabling two-factor authentication, and creating a wallet recovery seed. These steps will significantly enhance the security of your wallet and protect your funds from unauthorized access.
3. Keep Your Device Firmware Updated
Regularly updating your Trezor wallet’s firmware is essential to protect against potential security vulnerabilities. Firmware updates often include patches that address known security issues and improve overall performance. Check for firmware updates regularly and install them as soon as they become available.
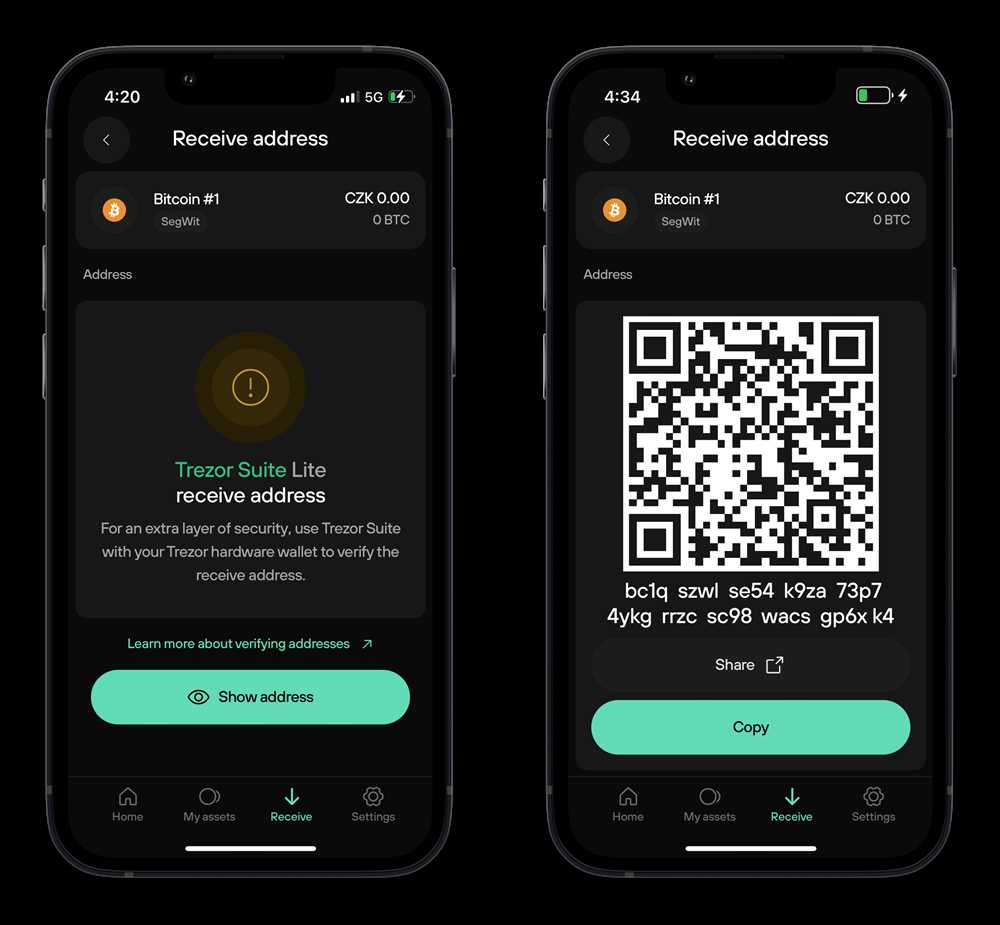
4. Verify Addresses on the Device

When making transactions with your Trezor wallet, always verify the recipient addresses directly on the device’s screen. This prevents the risk of address manipulation, where a malicious actor alters the address to divert your funds. Verifying addresses on the device ensures that you are sending your funds to the intended recipient.
5. Never Share your Recovery Seed

Your wallet recovery seed is a crucial component of your Trezor wallet’s security. Never share it with anyone and store it securely in offline, tamper-proof media. Sharing your recovery seed compromises the security of your wallet and allows unauthorized access to your funds.
By following these best practices, you can ensure the highest level of security when using a Trezor wallet. Implementing these measures will protect your funds from potential threats and give you peace of mind knowing that your cryptocurrency is securely stored.
Q&A:
What is Trezor Wallet?
Trezor Wallet is a hardware wallet that allows you to securely store your cryptocurrency offline.
How does Trezor Wallet work?
Trezor Wallet works by generating and storing your cryptocurrency private keys offline, away from potential security threats.
Can I use Trezor Wallet for multiple cryptocurrencies?
Yes, Trezor Wallet supports multiple cryptocurrencies including Bitcoin, Ethereum, and many others.
What are the security features of Trezor Wallet?
Trezor Wallet offers features such as a secure PIN code, passphrase encryption, and two-factor authentication to ensure the highest level of security for your cryptocurrency.


