
Exploring the Security of Trezor: Can It Get Infected with Malware?

In today’s digital age, protecting your cryptocurrency holdings is of the utmost importance. One popular hardware wallet that many cryptocurrency enthusiasts rely on is Trezor. It offers a secure and convenient way to store your digital assets offline. However, recent reports of potential malware threats targeting Trezor users have raised concerns about the security of this device. In this article, we will delve into the details of these reported threats and explore what steps you can take to ensure the safety of your Trezor wallet.
One of the main concerns regarding Trezor’s security is the possibility of firmware tampering. As a hardware wallet, Trezor employs firmware to operate and secure your funds. However, some malicious actors have attempted to exploit vulnerabilities in this firmware to gain unauthorized access to users’ wallets. This can potentially compromise the security of your digital assets and lead to devastating consequences.
To combat this threat, the team behind Trezor regularly releases firmware updates that address known vulnerabilities. It is crucial for users to regularly check for these updates and install them promptly to ensure the highest level of security. Additionally, Trezor recommends purchasing their devices directly from their official website or authorized resellers to minimize the risk of tampered firmware.
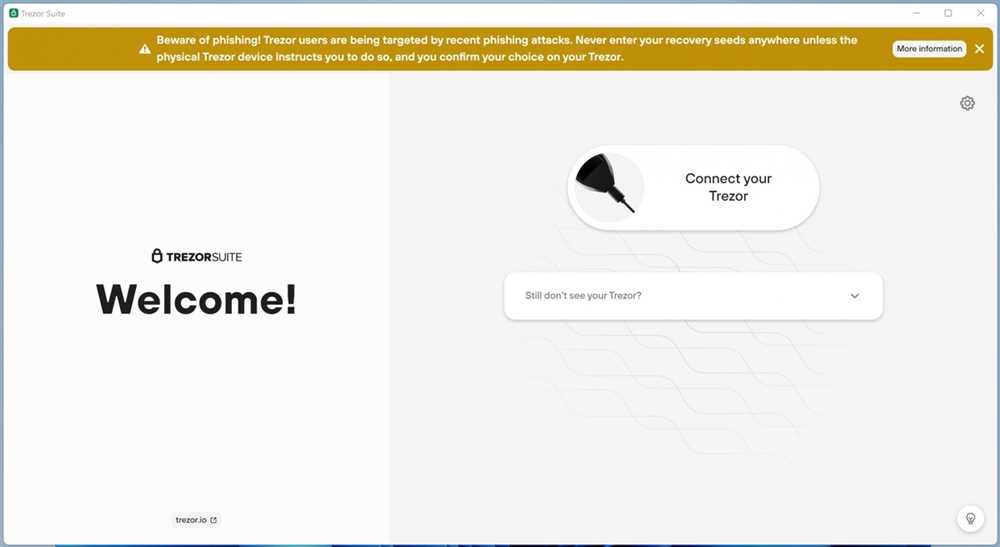
Another potential malware threat faced by Trezor users is the possibility of phishing attacks. Phishing is a method employed by cybercriminals to trick individuals into revealing their sensitive information, such as passwords or private keys. In the case of Trezor, scammers may create fake websites or applications that closely resemble the official Trezor interfaces, tricking users into providing their wallet credentials unknowingly.
To protect yourself from phishing attacks, it is crucial to remain vigilant and only access your Trezor wallet through official channels. Always double-check the URL of the website you are visiting and be cautious of any unsolicited messages or emails requesting your wallet information. Trezor also advises enabling the “U2F” feature, which adds an extra layer of security by requiring physical confirmation on supported platforms.
While the potential malware threats to Trezor users are a cause for concern, it is important to remember that no device or system is 100% secure. By staying informed about the latest security practices and regularly updating your firmware, you can greatly reduce the risk of falling victim to these threats. With the proper precautions and a proactive approach to security, you can continue to trust Trezor as an effective tool for safeguarding your cryptocurrency investments.
Is Your Trezor Secure?

In the world of cryptocurrency, security is of utmost importance. As more and more people start investing in digital assets, it becomes crucial to ensure the safety of your funds. One popular method of securing cryptocurrencies is by using a hardware wallet, such as Trezor.
Trezor is a hardware wallet that stores your private keys offline, away from potential online threats. It is designed to keep your funds secure by using advanced encryption algorithms and secure elements. However, despite its robust security features, no device is completely immune to potential malware threats.
Recently, there have been reports of malware designed specifically to target Trezor wallets. These malicious programs are often disguised as legitimate software updates or apps, leading unsuspecting users to unknowingly install them on their devices.
To ensure the security of your Trezor wallet, it is important to follow some best practices:
- Only download and install software updates from trusted sources. Avoid clicking on suspicious links or downloading files from unknown websites.
- Always verify the authenticity of the software update before installing it. Check for digital signatures and verify the source of the update.
- Enable two-factor authentication (2FA) to add an extra layer of security to your Trezor wallet.
- Regularly check for firmware updates from the official Trezor website and install them as soon as they are available.
- Consider using additional security measures like passphrase protection and PIN protection.
By following these best practices, you can minimize the risk of falling victim to potential malware threats. It is also important to stay informed about the latest security developments and vulnerabilities in the cryptocurrency world. Regularly check for updates and news from reliable sources to stay ahead of potential threats.
Remember, while Trezor offers strong security measures, it is ultimately up to the user to take responsibility for the safety of their funds. By following best practices and staying vigilant, you can feel confident in the security of your Trezor wallet.
Investigating Potential Malware Threats
In the digital age, cybersecurity is of utmost importance, especially when it comes to protecting sensitive financial information. As cryptocurrency gains popularity, securing your digital assets becomes even more critical. Trezor, one of the most popular hardware wallets, provides an extra layer of security to ensure the safety of your funds. However, it is essential to stay vigilant and aware of potential malware threats that may compromise your Trezor device.
Recognizing the Risks
- Phishing Attacks: Malicious actors often try to deceive individuals into providing their confidential information through phishing attacks. These attacks typically involve fraudulent emails or websites that imitate legitimate sources. By tricking users into revealing their Trezor recovery seed or private keys, hackers gain access to their digital assets.
- Supply Chain Attacks: Malware can be introduced into the supply chain during the manufacturing process. This attack involves compromising hardware devices during production or delivery. Subsequently, the compromised device can be used to extract sensitive information, such as private keys, compromising the security of the user’s funds.
- Firmware Manipulation: Malware can also be embedded within the firmware of a Trezor device. This type of attack allows hackers to manipulate the device’s functionality, potentially stealing the user’s private keys or sending funds to unauthorized recipients.
Protection Measures

To ensure the security of your Trezor device and funds, it is vital to take precautionary measures:
- Always obtain your Trezor device directly from the official website or authorized resellers to minimize the risk of supply chain attacks.
- Regularly check the official Trezor website for firmware updates and install them promptly to stay protected against potential vulnerabilities.
- Never share your recovery seed or private keys with anyone and be cautious of phishing attempts via emails or websites imitating Trezor or other trusted sources.
- Keep your computer’s antivirus software up to date and scan your device regularly to detect any potential malware threats.
- Consider implementing additional security measures, such as passphrase protection or using multi-signature transactions for enhanced security.
By following these steps, you can significantly reduce the risk of falling victim to malware threats and ensure the safety of your digital assets stored on your Trezor device.
Understanding the Risks
When it comes to securing your cryptocurrencies, it is important to be aware of the potential risks that may arise. While technologies like Trezor provide a high level of security, there are still some factors that you should consider.
Malware threats: One of the main risks is the possibility of malware infecting your computer or mobile device. Malicious software can be designed to intercept and steal your cryptocurrency information, including your private keys. It is important to use antivirus software and keep your operating system and applications up to date to minimize this risk.
Phishing attacks: Phishing is a common technique used by cybercriminals to trick users into revealing their sensitive information, such as passwords and private keys. They often create fake websites or send misleading emails that appear to be from legitimate sources. It is important to always double-check the URLs you are visiting and never provide your private keys or passwords unless you are certain about the source’s authenticity.
Physical theft: Although Trezor provides offline storage for your private keys, physical theft of your device is still a risk to consider. If an unauthorized person gains access to your Trezor, they may be able to extract your private keys and access your funds. It is essential to keep your device in a secure location and make use of additional security measures like a PIN or passphrase.
Human error: Even with advanced security measures in place, human error can still lead to the loss of cryptocurrencies. It is important to double-check the addresses when sending funds and ensure you have backed up your private keys in a secure location. Additionally, being cautious of suspicious links and attachments can help avoid falling victim to phishing attacks.
Data loss: Losing access to your private keys can result in permanent loss of your cryptocurrencies. It is crucial to regularly back up your private keys and ensure you have multiple copies stored in secure locations. Consider using different backup methods, such as writing down your keys on a piece of paper or using encrypted digital storage.
Regulatory risks: Cryptocurrencies are subject to regulatory changes, which can impact their value and accessibility. Government regulations and restrictions may affect your ability to use or trade cryptocurrencies. Staying informed about the legal and regulatory landscape can help you make better decisions and mitigate potential risks.
By understanding these risks and taking necessary precautions, you can enhance the security of your Trezor and protect your cryptocurrencies.
Protecting Your Trezor
When it comes to securing your Trezor device, there are several steps you can take to protect your assets and minimize the risk of potential malware threats. Here are some tips to follow:
1. Purchase from an Authorized Reseller

Make sure to buy your Trezor device from an authorized reseller to ensure its authenticity. Avoid purchasing from unknown or untrusted sources, as counterfeit devices may come preloaded with malware.
2. Check for Tampering
Before using your Trezor, inspect it for any signs of tampering, such as broken seals or visibly damaged packaging. If you notice anything suspicious, contact the manufacturer immediately for assistance.
3. Keep Firmware Updated
Regularly check for firmware updates and install them promptly. These updates often include security patches that address known vulnerabilities and protect against emerging threats.
4. Enable Wallet Passphrase
Consider enabling a wallet passphrase feature offered by Trezor. This additional layer of security requires you to enter a custom passphrase every time you access your wallet, adding another barrier against potential attacks.
5. Use Strong and Unique PIN
Choose a PIN for your Trezor wallet that is at least 8 characters long and consists of a combination of letters, numbers, and special characters. Avoid using common passcodes or easily guessable patterns.
6. Be Wary of Phishing Attempts
Be cautious of phishing attempts that may try to trick you into disclosing sensitive information, such as your recovery seed or PIN. Always verify the authenticity of messages or websites before providing any personal details.
By following these guidelines, you can significantly enhance the security of your Trezor device and protect your digital assets from potential malware threats.
Best Practices for Secure Cryptocurrency Storage

With the increasing popularity of cryptocurrencies like Bitcoin, it’s becoming more important than ever to ensure the security of your digital assets. Here are some best practices to follow for secure cryptocurrency storage:
1. Use a Hardware Wallet
A hardware wallet, such as Trezor, is one of the safest ways to store your cryptocurrency. It keeps your private keys offline, reducing the risk of being hacked or infected with malware. Make sure to purchase your hardware wallet from a reputable source to avoid counterfeit devices.
2. Enable Two-Factor Authentication
Adding an extra layer of security by enabling two-factor authentication (2FA) can help protect your cryptocurrency from unauthorized access. Use 2FA methods like a mobile app or hardware token instead of SMS-based authentication, which can be vulnerable to SIM swapping attacks.
3. Update Wallet Software Regularly
Wallet software updates often include important security fixes and enhancements. Stay up to date by regularly checking for updates and installing them as soon as they become available. This will help prevent known vulnerabilities from being exploited.
4. Implement Strong Passwords

Using a strong, unique password is essential for securing your cryptocurrency. Avoid using easily guessable passwords or reusing passwords across multiple platforms. Consider using a password manager to generate and store complex passwords.
5. Backup Your Wallet

Make regular backups of your wallet and store them securely in offline locations. This way, if your hardware wallet is lost or damaged, you can easily recover your funds. Use encrypted storage and consider using multiple backup locations to reduce the risk of data loss.
| 6. Be Cautious of Phishing Attempts | 7. Practice Safe Online Behavior |
|---|---|
| Double-check the website addresses and avoid clicking on suspicious links or downloading files from unknown sources. Phishing attempts are common in the cryptocurrency space, and falling for them can lead to loss of funds. | Avoid using public Wi-Fi networks when accessing your cryptocurrency wallets or making transactions. Keep your operating system and antivirus software up to date to prevent malware infections. Consider using a dedicated device for your cryptocurrency activities. |
By following these best practices, you can significantly enhance the security of your cryptocurrency storage and protect your digital assets from potential threats.
Q&A:
What is Trezor?
Trezor is a hardware wallet designed to securely store cryptocurrencies.
How does Trezor protect my cryptocurrencies?
Trezor uses a combination of encryption and offline storage to protect your cryptocurrencies from hackers.
Can malware compromise the security of my Trezor?
While it is technically possible for malware to compromise the security of a Trezor, it is highly unlikely if you follow the recommended security practices.
What are some potential malware threats to Trezor?
Some potential malware threats to Trezor include keyloggers, screen capture malware, and malware that alters the address displayed on the screen.
How can I protect my Trezor from malware threats?
To protect your Trezor from malware threats, make sure to always verify the address shown on the screen, use a secure computer, and keep your firmware up to date.


